Answered step by step
Verified Expert Solution
Question
1 Approved Answer
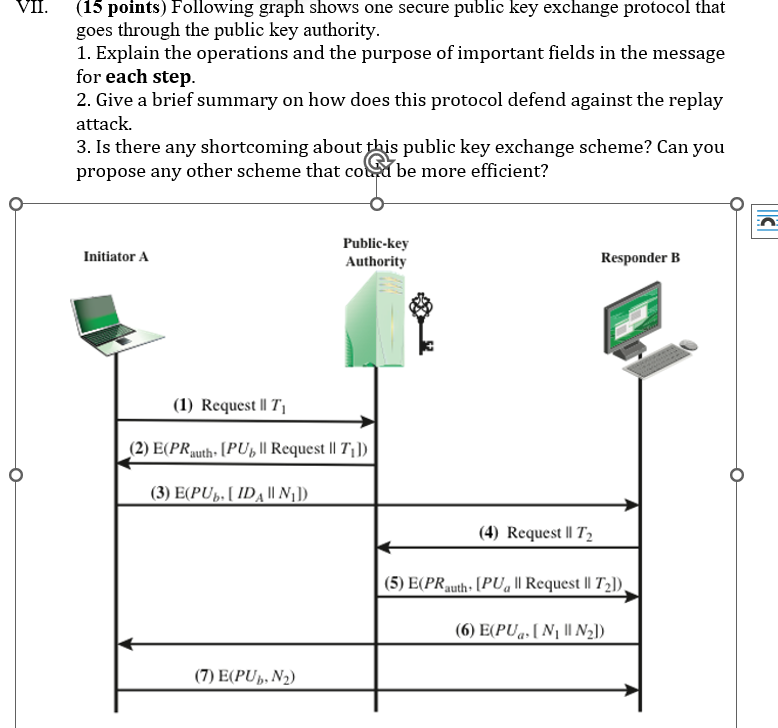
VII. ( 1 5 points ) Following graph shows one secure public key exchange protocol that goes through the public key authority. Explain the operations
VII. points Following graph shows one secure public key exchange protocol that
goes through the public key authority.
Explain the operations and the purpose of important fields in the message
for each step.
Give a brief summary on how does this protocol defend against the replay
attack.
Is there any shortcoming about this public key exchange scheme? Can you
propose any other scheme that co Ge more efficient?
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started