Answered step by step
Verified Expert Solution
Question
1 Approved Answer
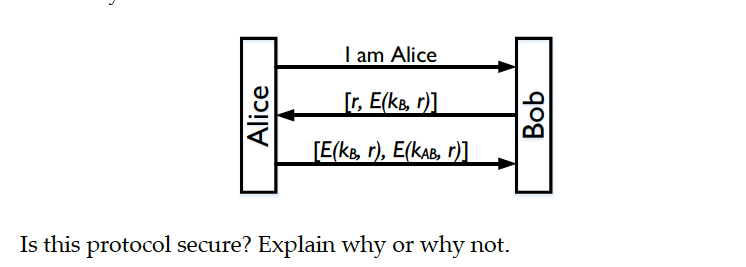
we show an authentication protocol for the stateless server Bob to authenticate a user Alice, which is not secure. Now let's modify the protocol as
we show an authentication protocol for the stateless server Bob to authenticate a user Alice, which is not secure. Now let's modify the protocol as follows: Bob is still a stateless server and it sends both a challenge, and the challenge encrypted with a key that only he knows, to Alice. Alice then sends the received encrypted challenge back to Bob, together with the same challenge encrypted with the shared secret key between Alice and Bob
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


