Question: What kind of security threat involves a hacker obtaining administrator-level access to a computer or network? O Trojan Worm Rootkit What is the first
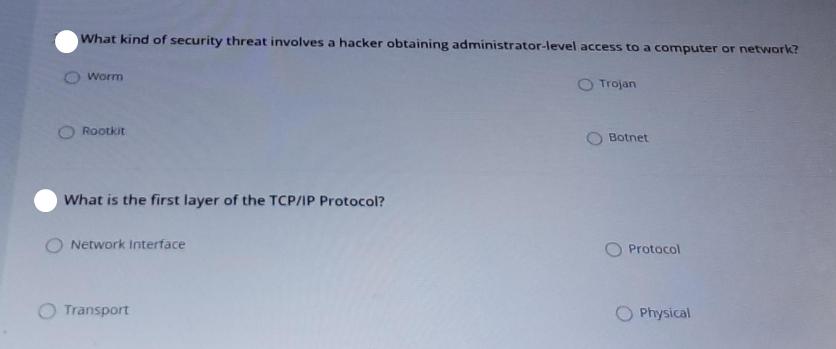
What kind of security threat involves a hacker obtaining administrator-level access to a computer or network? O Trojan Worm Rootkit What is the first layer of the TCP/IP Protocol? Network Interface Transport Botnet Protocol Physical
Step by Step Solution
3.44 Rating (163 Votes )
There are 3 Steps involved in it
The detailed answer for the above question is provided below The image presents two multiplechoice q... View full answer

Get step-by-step solutions from verified subject matter experts


