Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Which of the following is true about using the MD 5 hash to authenticate encrypted messages? a . It is considered secure for authentication and
Which of the following is true about using the MD hash to authenticate encrypted messages? a It is considered secure for authentication and is still in use. b There are theoretical ways to create collisions for MD but these have not been replicated in the real world. Since the attacks are only theoretical MD is still considered safe to use for authentication. c MD is considered broken because it is not collision resistant, and it should not be used for authentication. d MD is considered broken and should not be used for aThe MD hash is considered broken, since collisions have been found
and, in fact, a collision can be constructed in a few seconds on a PC
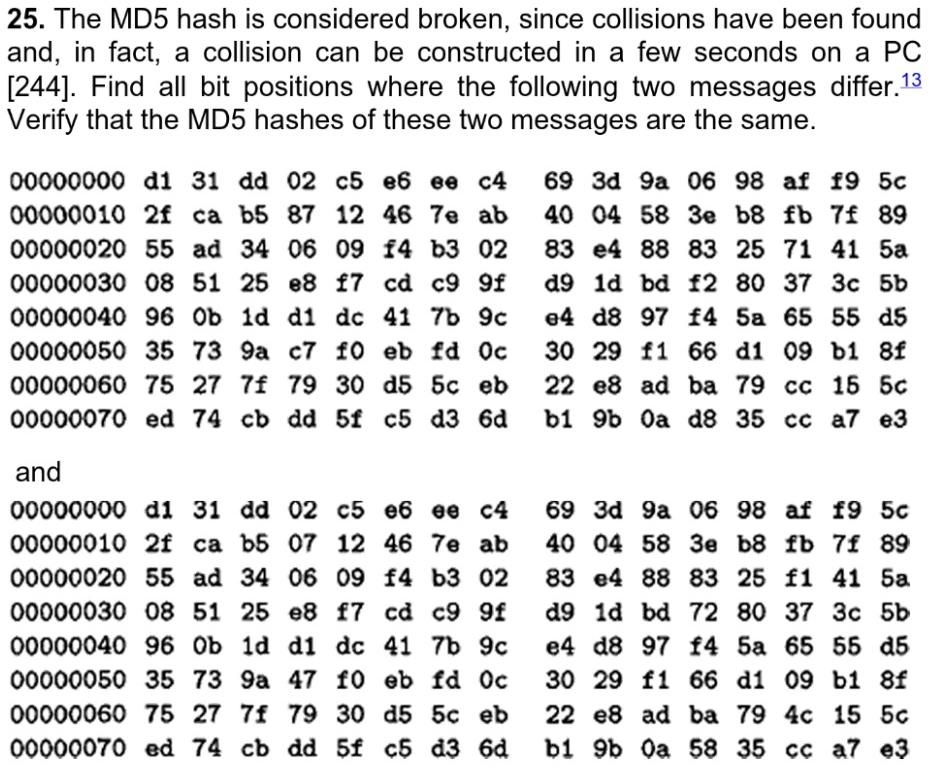
Find all bit positions where the following two messages differ.
Verify that the MD hashes of these two messages are the same.
and
di dd c e ee cd a af af c
e f cd c f d bd
ob d d dc b c e d fa d
fo eb fd f d b
d eb e ad ba
ed dd c dd bb a cc a euthentication. MD and MD are still considered secure and are still in use. e None of the above
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


