Answered step by step
Verified Expert Solution
Question
1 Approved Answer
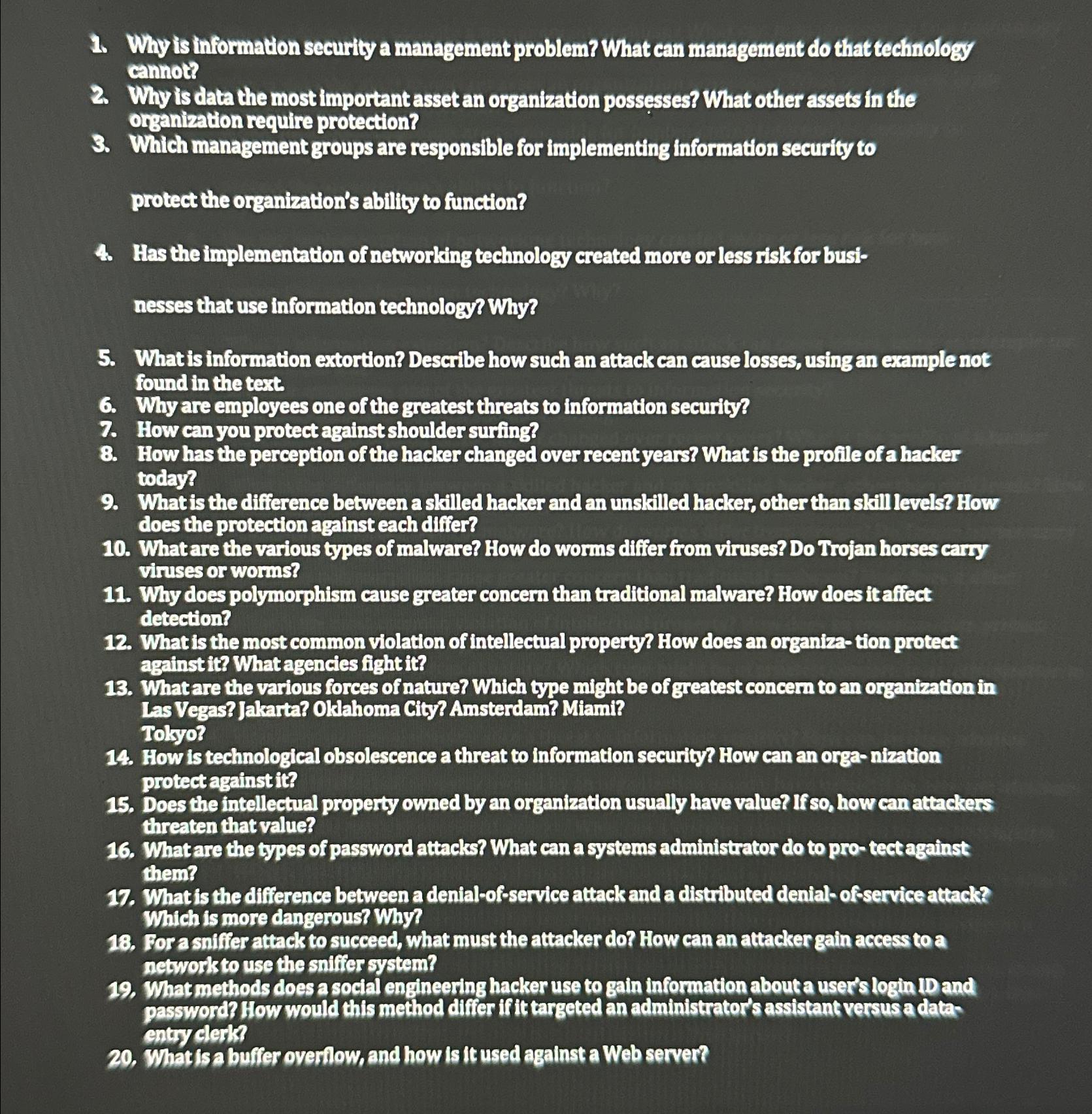
Why is information security a management problem? What can management do that technology cannot? Why is data the most important asset an organization possesses? What
Why is information security a management problem? What can management do that technology cannot?
Why is data the most important asset an organization possesses? What other assets in the organization require protection?
Which management groups are responsible for implementing information security to
protect the organization's ability to function?
Has the implementation of networking technology created more or less risk for businesses that use information technology? Why?
What is information extortion? Describe how such an attack can cause losses, using an example not found in the text.
Why are employees one of the greatest threats to information security?
How can you protect against shoulder surfing?
How has the perception of the hacker changed over recent years? What is the profile of a hacker today?
What is the difference between a skilled hacker and an unskilled hacker, other than skill levels? How does the protection against each differ?
What are the various types of malware? How do worms differ from viruses? Do Trojan horses carry viruses or worms?
Why does polymorphism cause greater concern than traditional malware? How does it affect detection?
What is the most common violation of intellectual property? How does an organiza tion protect againstit? What agencies fight it
What are the various forces of nature? Which type might be of greatest concern to an organization in Las Vegas? Jakarta? Oklahoma City? Amsterdam? Miami? Tokyo?
How is technological obsolescence a threat to information security? How can an organization protect againstit?
Does the intellectual property owned by an organization usually have value? If so how can attackers threaten that value?
What are the types of password attacks? What can a systems administrator do to protect against them?
What is the difference between a denialofservice attack and a distributed denialofservice attack? Which is more dangerous? Why?
For a suiffer attack to succeed, what must the attacker do How can an attacker gain access to a network to use the sniffer system?
What methods does a social engineering hacker use to gain information about a user's login ID and password? How would this method differ if it targeted an administrator's assistant versus a data: entry clerk?
What is a buffer overflow, and how is it used against a Web server?
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


