Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Why is it risky if you wanted to make an exception to the application policy to allow file sharing software? The software can shrink attack
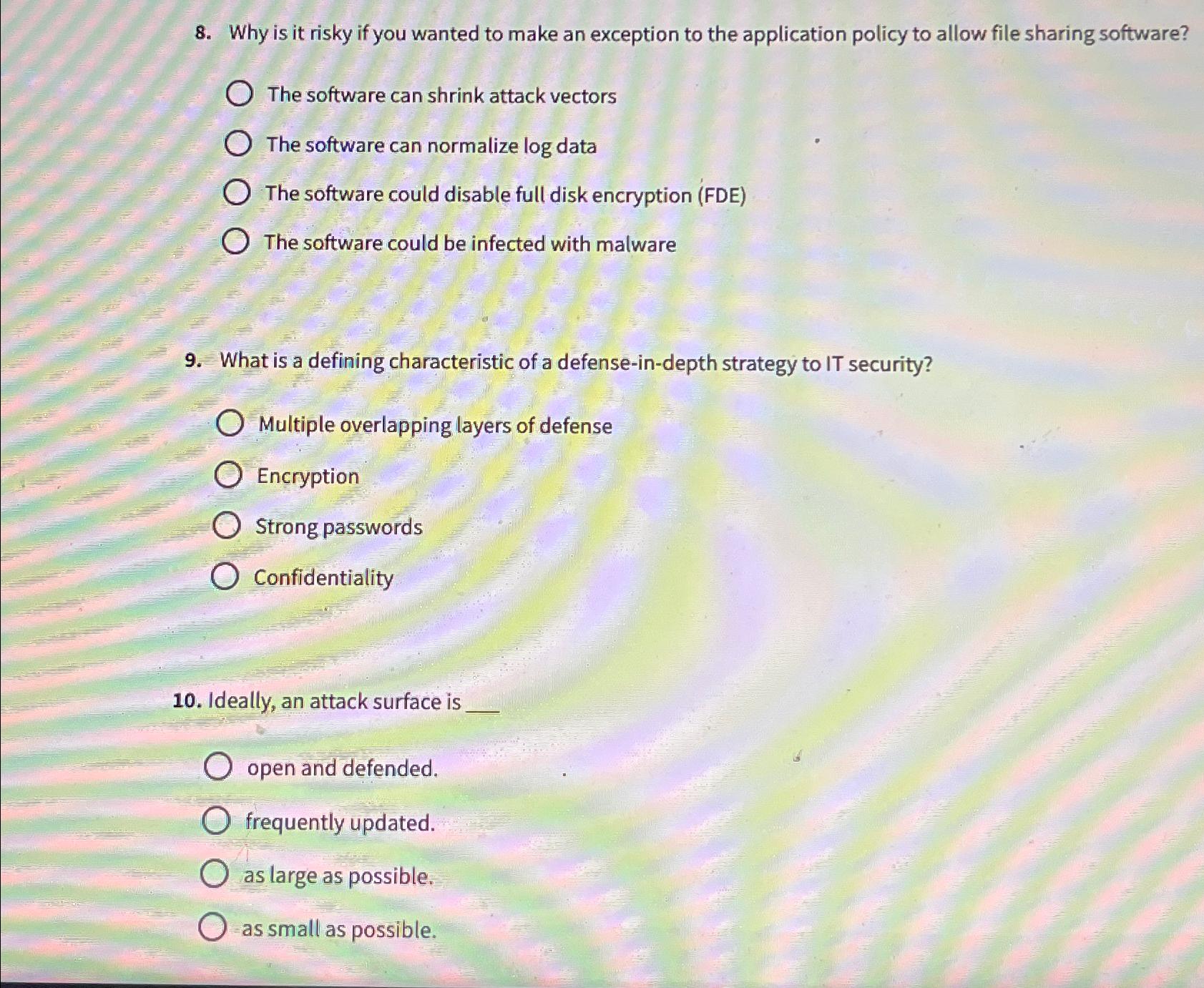
Why is it risky if you wanted to make an exception to the application policy to allow file sharing software?
The software can shrink attack vectors
The software can normalize log data
The software could disable full disk encryption FDE
The software could be infected with malware
What is a defining characteristic of a defenseindepth strategy to IT security?
Multiple overlapping layers of defense
Encryption
Strong passwords
Confidentiality
Ideally, an attack surface is
open and defended.
frequently updated.
as large as possible.
as small as possible.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started