Answered step by step
Verified Expert Solution
Question
1 Approved Answer
You have been hired as a threat detection analyst for a bank. Part of your job is inspecting IP logs to try to find any
You have been hired as a threat detection analyst for a bank. Part of your job is inspecting IP logs
to try to find any potential security threats.
An IP version address contains octets of numbers between and They are in a format
such as:
For purposes of this lab, all the IPv addresses have the full octet, even if the number starts with
As such, would be stored as
Professor Offenberg teaches an excellent Ethical Hacking class here at HCC Unfortunately, his
evil twin brother, Darth Offenberg, is the head of the international crime group Offenberg's
Unethical Computer Hackers OUCH Hackers from OUCH are trying to penetrate your system.
OUCH always begin with one of three IP address ranges in the first two octets:
You have been forwarded a file called "ipfile.txt This file contains an unknown number of IP
addresses and the data and time that the IP address accessed your system. Your job is to read
the file, find all the suspect IP addresses that might have been used by OUCH, and produce an
output report to both the screen and to an output file.
The program must allow the user to enter in the name of the input file:
a The program must call a function that receives the input filename as a parameter
b The program must use a try..except block to test that the file exists; if it does not
exist, the program must display the appropriate error message and allow the
reentry of the filename
c Once the program determines that the file exists, the function must return the file
handle
The program must allow the user to enter in the name of the output file:
a The program must call the same function as above that recieives the output
filename as a parameter
b The program must use a try..except block to test that the file can be crated; if it
cannot be created, the program must display the appropriate error message and
allow the reentry of the filename
c Once the program determines that the file can be created, the function must
return the file handle
The program must read all the data in the input file as strings:
a The program must keep a count of the total number of records in the file
b The program must create a list of strings that contains all the suspect IP Addresses;
these are IP addresses that start with the values listed above
c Once the entire file is read, the program must close the file
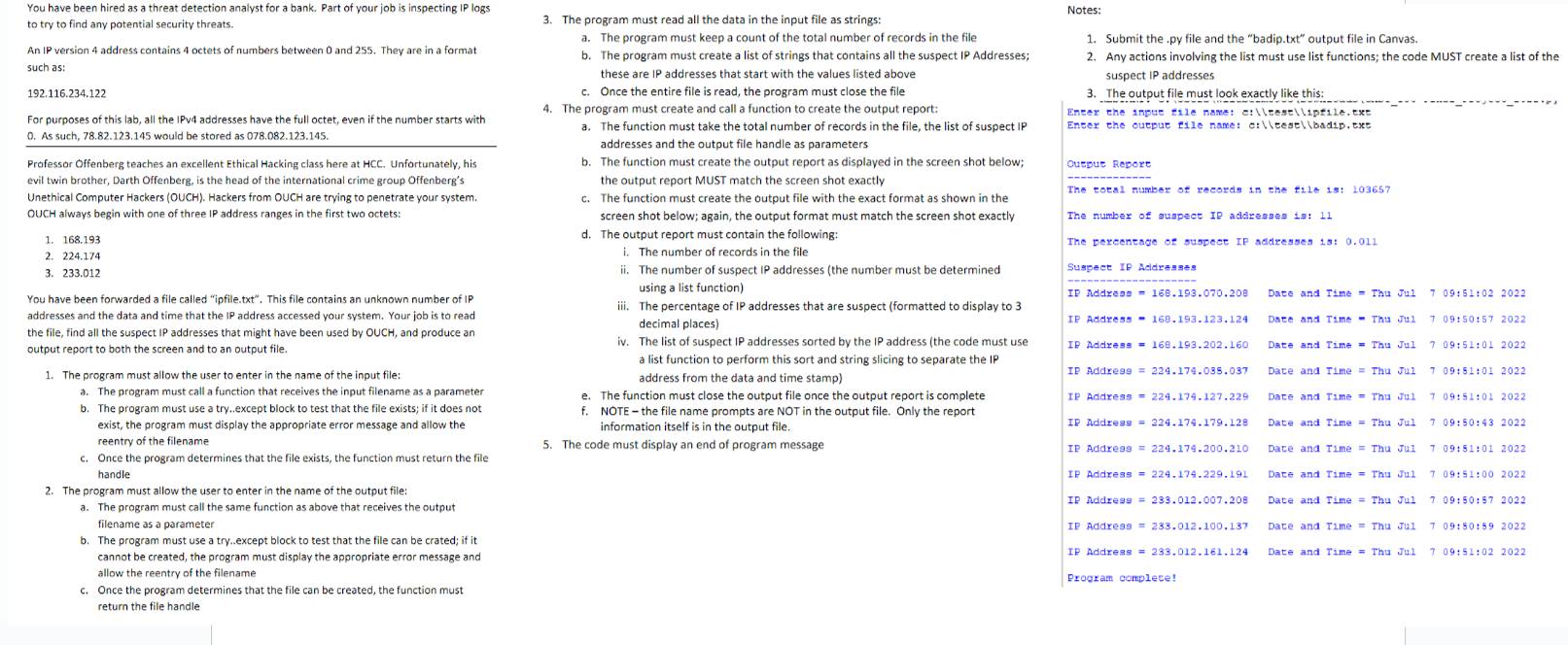
The program must create and call a function to create the output report:
a The function must take the total number of records in the file, the list of suspect IP
addresses and the output file handle as parameters
b The function must create the output report as displayed in the screen shot below;
the output report MUST match the screen shot exactly
c The function must create the output file with the exact format as shown in the
screen shot below; again, the output format must match the screen shot exactly
d The output report must contain the following:
i The number of records in the file
ii The number of suspect IP addresses the number must be determined
using a list function
iii. The percentage of addresses that are suspect formatted to display to
decimal places
iv The list of suspect IP addresses sorted by the IP address the code must use
a list function to perform this sort and string slicing to separate the IP
address from the data and time stamp
e The function must close the output file once the output report is complete
f NOTE the file name prompts are NOT in the output file. Only the report
information itself is in the output file.
The code must display an end of program message
Notes:
Submit the py file and the "badip.txt output file in Canvas.
Any actions involving the list must use list functions; the code MUST create a list of the
suspect IP addresses
The output file must look exactly like this:
Encer the ouepue tile name: c:lleesellbadip. ext
Outpue Report
The rotal number of records in the fe :
The number of augpect Ip addresges is:
The percentage of suspect IP addresses s:
Sugpect If Acleresses
If Address Dace and Time Thu Jul ::
IP Address Dse and Time Thu Ju::
If Address Date and Time Thu Jul ::
IP Address Dace and Time Thu Ju::
IP Andress Dace and Tme Thu Ju::
IP Addregs Date and Time Thu Jul ::
IP Address Dace and Time Thu Ju
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started