Question: For the following C code, the expressions val1val4 all map to the program values i, f, d, and l: double fcvt2(int *ip, float *fp, double
For the following C code, the expressions val1–val4 all map to the program values i, f, d, and l:
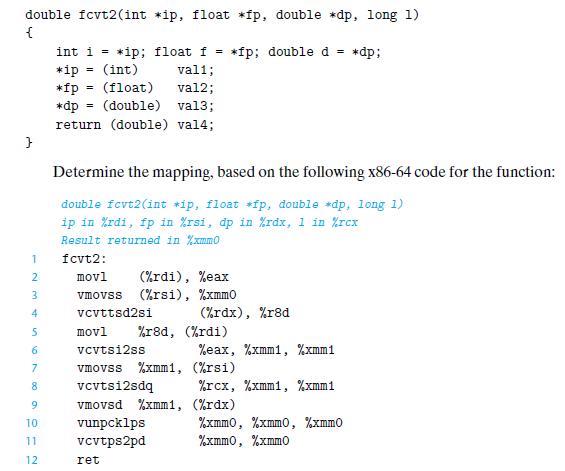
double fcvt2(int *ip, float *fp, double *dp, long 1) { } 1 2 3 4 5 6 7 8 9 10 11 12 int i = *ip; float f = *ip (int) *fp (float) *dp = (double) vali; val2; val3; return (double) val4; = = movl vcvtsi2ss vmovss %xmm1, Determine the mapping, based on the following x86-64 code for the function: double fcvt2(int *ip, float *fp, double *dp, long 1) ip in %rdi, fp in %rsi, dp in %rdx, 1 in /rcx Result returned in %xmm0 fcvt2: movl (%rdi), %eax vmovss (%rsi), %xmmo vcvttsd2si %r8d, (%rdi) *fp; double d vunpcklps vcvtps2pd ret (%rdx), %r8d %eax, %xmm1, %xmm1 (%rsi) vcvtsi2sdq vmovsd %xmm1, (%rdx) %rcx, %xmm1, %xmm1 = *dp; %xmmo, %xmmo, %zmmo %xmmo, %xmmo
Step by Step Solution
3.38 Rating (148 Votes )
There are 3 Steps involved in it
This exercise requires that you step through the code paying careful att... View full answer

Get step-by-step solutions from verified subject matter experts


