The following poorly written e-mail tells customers that their e-mail addresses have been hacked. However, the message
Question:
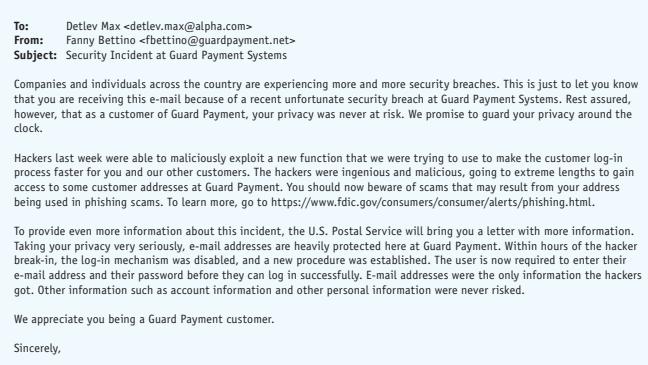
The following poorly written e-mail tells customers that their e-mail addresses have been hacked. However, the message is clumsy and fails to include essential information in revealing security breaches to customers.
Your Task.
Analyze the message and list at least five weaknesses. If your instructor directs, revise it using the suggestions you learned in this chapter about security breach messages.
Transcribed Image Text:
To: Detlev Max From: Fanny Bettino Subject: Security Incident at Guard Payment Systems Companies and individuals across the country are experiencing more and more security breaches. This is just to let you know that you are receiving this e-mail because of a recent unfortunate security breach at Guard Payment Systems. Rest assured, however, that as a customer of Guard Payment, your privacy was never at risk. We promise to guard your privacy around the clock. Hackers last week were able to maliciously exploit a new function that we were trying to use to make the customer log-in process faster for you and our other customers. The hackers were ingenious and malicious, going to extreme lengths to gain access to some customer addresses at Guard Payment. You should now beware of scams that may result from your address being used in phishing scams. To learn more, go to https://www.fdic.gov/consumers/consumer/alerts/phishing.html. To provide even more information about this incident, the U.S. Postal Service will bring you a letter with more information. Taking your privacy very seriously, e-mail addresses are heavily protected here at Guard Payment. Within hours of the hacker break-in, the log-in mechanism was disabled, and a new procedure was established. The user is now required to enter their e-mail address and their password before they can log in successfully. E-mail addresses were the only information the hackers got. Other information such as account information and other personal information were never risked. We appreciate you being a Guard Payment customer. Sincerely,
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 0% (1 review)
Analyzing the provided email there are several weaknesses that can be identified in its communication about the security breach 1 Lack of Clarity and Urgency The email does not clearly state the probl...View the full answer

Answered By

Sumit kumar
Education details:
QUATERNARY Pursuing M.Tech.(2017-2019) in Electronics and Communication Engg. (VLSI DESIGN) from
GNIOT Greater Noida
TERTIARY B.Tech. (2012-2016) in Electronics and Communication Engg. from GLBITM Greater Noida
SECONDARY Senior Secondary School Examination (Class XII) in 2012 from R.S.S.Inter College, Noida
ELEMENTARY Secondary School Examination (Class X) in 2010 from New R.J.C. Public School ,Noida
CERTIFICATION
Summer Training in ‘WIRELESS EMBEDDED SYSTEM’ from ‘XIONEE’ for the six weeks.
EMBEDDED SYSTEM Certificate issued by CETPA INFOTECH for one day workshop.
Certificate of Faculty development program on OPTICAL COMMUNICATION and NETWORKS for one week.
5.00+
1+ Reviews
10+ Question Solved
Related Book For 

Essentials Of Business Communication
ISBN: 9780357714973
12th Edition
Authors: Mary Ellen Guffey, Dana Loewy
Question Posted:
Students also viewed these Business questions
-
The following poorly written e-mail tells customers that their e-mail addresses have been hacked. However, the message is clumsy and fails to include essential information in revealing security...
-
The following message responds to the inquiry in Radical Rewrite 6.1. Dr. Chen asks for information about dealing with a data breach at his medical firm. Mr. Vance, from Security Specialists, wants...
-
The following e-mail message from Kennedy Freed asks his assistant Camille Chavez to perform a task. However, she will struggle with that task because the message is so poorly written. It badly needs...
-
Shoppers enter Hamilton Place Mall at an average of 120 per hour. What is the probability that at least 35 shoppers will enter the mall between 5:00 and 5:10 pm?
-
A liquid jet of density r and area A strikes a block and splits into two jets, as shown in the figure. All three jets have the same velocity V. The upper jet exits at angle θ and area αA,...
-
At a crime scene, the forensic investigator notes that the 8.2-g lead bullet that was stopped in a doorframe apparently melted completely on impact. Assuming the bullet was fired at room temperature...
-
(Appendix 1A) Briefly differentiate among a sole proprietorship, a partnership, and a corporation.
-
Anthony, CPA, prepared the flowchart (p. 330) which portrays the raw materials purchasing function of one of Anthony's clients, Medium-Sized Manufacturing Company, from the preparation of initial...
-
Udeagbalas institutional shareholders invest in a widerange of entities. Udeagbalas directors are concerned that certain IFRS and IAS Standards permit entities to choose between different measurement...
-
Having enjoyed a meteoric rise, CompuBotics Incorporated prides itself on its commitment to employees who receive generous benefits and are steeped in a supportive corporate culture. This core value...
-
The following blunt refusal from a restaurant owner rejects a previously agreed-to favor. To avoid endangering a friendship and losing community goodwill, the writer needs to revise this message....
-
z = 1.5 for H a : > 0.227 Find the P-value that corresponds to the standard z-score, and determine whether the alternative hypothesis is supported at the 0.05 significance level.
-
What is the standard federal NOL carryback/carryforward period and how do states differ?
-
Medical Instruments produces a variety of electronic medical devices. Medical Instruments uses a standard cost system and computes price variances at the time of purchase. One product, a digital...
-
At the beginning of the year, a university sets standards for processing 1,000 admissions applications with 10,000 direct labor hours. The application rate for overhead is 40 per standard direct...
-
How would you describe, in one sentence, each of the following accounting principles, concepts and constraints? Accounting entity Accounting period Monetary unit Cost-benefit Going concern...
-
To manufacture its main product, a firm requires a standard of 10 direct labor hours per unit. The standard labor rate is \($20\) per hour. The product requires a standard of 25 kilograms of...
-
1. What trade- offs are involved in deciding to have a single large, centrally located facility instead of several smaller, dispersed facilities? 2. Who needs to be involved in facility location...
-
Find the intercepts and then graph the line. (a) 2x - 3y = 6 (b) 10 - 5x = 2y
-
1. Compare the advantages and disadvantages of searching for jobs at big board sites, such as Monster.com , with searching at company Web sites. 2. Why would companies ask job applicants to comment...
-
Insecure entry-level workers are not the only job seekers who sometimes feel tempted to fudge the facts. RadioShacks CEO David Edmondson had to resign after it was found that he had incorrectly...
-
Advice columns and Internet blogs are teeming with cover letter bloopers. Downright lies aside, some candidates simply need a lesson in selling: P.S. I havent taken a sick day in years; I dont get...
-
Exercise 3 - 1 5 A ( Algo ) Multiple product break - even analysis LO 3 - 6 Franklin Company manufactures two products. The budgeted per - unit contribution margin for each product follows: Franklin...
-
Jacob was hired as the Chief Marketing Officer (CMO) of Theta Corporation, a publicly-traded company in the retail sector, effective July 1, 2022. Throughout the fiscal year 2023, Theta Corporation...
-
Your company has purchased a large new truck - tractor for over - the - road use ( asset class 0 0 . 2 6 ) . It has a cost basis of $ 1 8 0 , 0 0 0 . With additional options costing $ 1 5 , 0 0 0 ....

Study smarter with the SolutionInn App