1 a. Please use given case study "Hospital laptop goes missing" and prepare an appropriate detailed Network Forensic Report.
b. Provide a summary of the security problems from a stolen laptop and its and potential risks
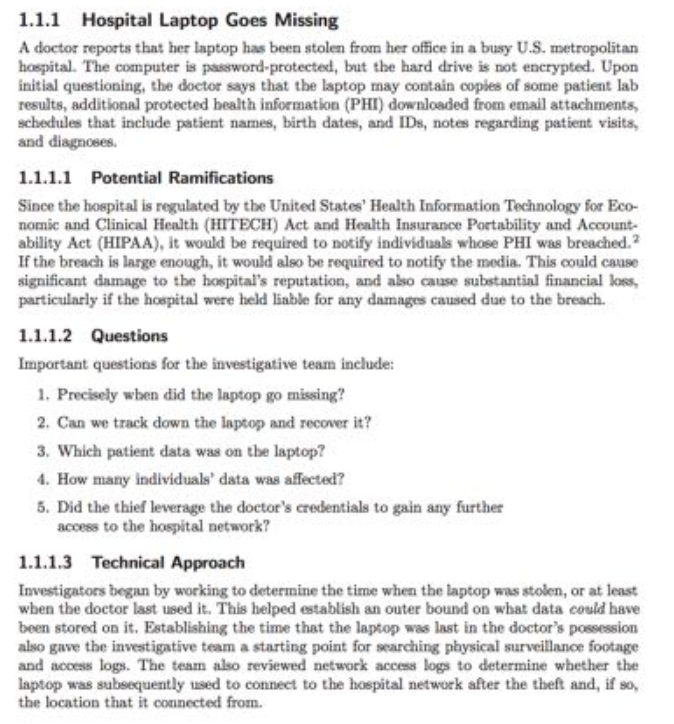

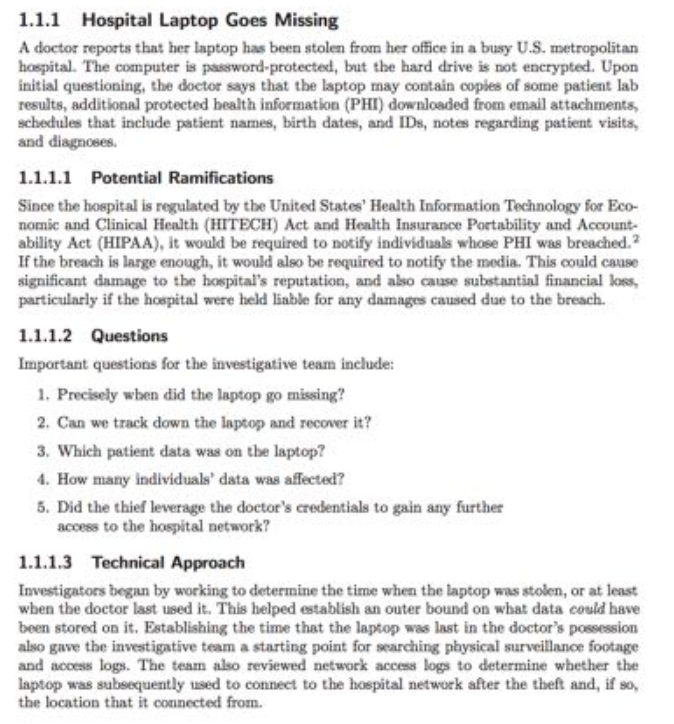
1.1.1 Hospital Laptop Goes Missing A doctor reports that her laptop has been stolen from her office in a busy U.S. metropolitan hospital. The computer is password-protected, but the hard drive is not encrypted. Upon initial questioning, the doctor says that the laptop may contain copies of some patient lab results, additional protected bealth information (PHI) downloaded from email attachments schedules that include patient names, birth dates, and IDs, notes regarding patient visits, and diagnoses. 1.1.1.1 Potential Ramifications Since the hospital is regulated by the United States' Health Information Technology for Eco- nomic and Clinical Health (HITECH) Act and Health Insurance Portability and Account- ability Act (HIPAA), it would be required to notify individuals whose PHI was breached.2 If the breach is large enough, it would also be required to notify the media. This could cause significant damage to the hospital's reputation, and also cause substantial financial loss particularly if the hospital were held liable for any damages caused due to the breach. 1.1.1.2 Questions Important questions for the investigative team include: 1. Precisely wben did the laptop go missing? 2. Can we track down the laptop and recover it? 3. Which patient data was on the laptop? . How many individuals' data was affected? 5. Did the thief leverage the doctor's credentials to gain any further access to the hospital network? 11.1.3 Technical Approach Investigators began by working to determine the time when the laptop was stolen, or at least wben the doctor last used it. This helped establish an outer bound on what data could have been stored on it. Establishing the time that the laptop was last in the doctor's possession also gave the investigative team a starting point for searching physical surveillance footage and acoess logs. The team also reviewed network access logs to determine whether the laptop was subsequently used to connect to the hospital network after the theft and, if so, the location that it connected from 1.1.1 Hospital Laptop Goes Missing A doctor reports that her laptop has been stolen from her office in a busy U.S. metropolitan hospital. The computer is password-protected, but the hard drive is not encrypted. Upon initial questioning, the doctor says that the laptop may contain copies of some patient lab results, additional protected bealth information (PHI) downloaded from email attachments schedules that include patient names, birth dates, and IDs, notes regarding patient visits, and diagnoses. 1.1.1.1 Potential Ramifications Since the hospital is regulated by the United States' Health Information Technology for Eco- nomic and Clinical Health (HITECH) Act and Health Insurance Portability and Account- ability Act (HIPAA), it would be required to notify individuals whose PHI was breached.2 If the breach is large enough, it would also be required to notify the media. This could cause significant damage to the hospital's reputation, and also cause substantial financial loss particularly if the hospital were held liable for any damages caused due to the breach. 1.1.1.2 Questions Important questions for the investigative team include: 1. Precisely wben did the laptop go missing? 2. Can we track down the laptop and recover it? 3. Which patient data was on the laptop? . How many individuals' data was affected? 5. Did the thief leverage the doctor's credentials to gain any further access to the hospital network? 11.1.3 Technical Approach Investigators began by working to determine the time when the laptop was stolen, or at least wben the doctor last used it. This helped establish an outer bound on what data could have been stored on it. Establishing the time that the laptop was last in the doctor's possession also gave the investigative team a starting point for searching physical surveillance footage and acoess logs. The team also reviewed network access logs to determine whether the laptop was subsequently used to connect to the hospital network after the theft and, if so, the location that it connected from