Answered step by step
Verified Expert Solution
Question
1 Approved Answer
1. Decrypt the ciphertext ERTWZSECXNPSWMEVTDR, which was encrypted using the key PAPER 2. Encrypt the messages cook and book using the Hill cipher with m
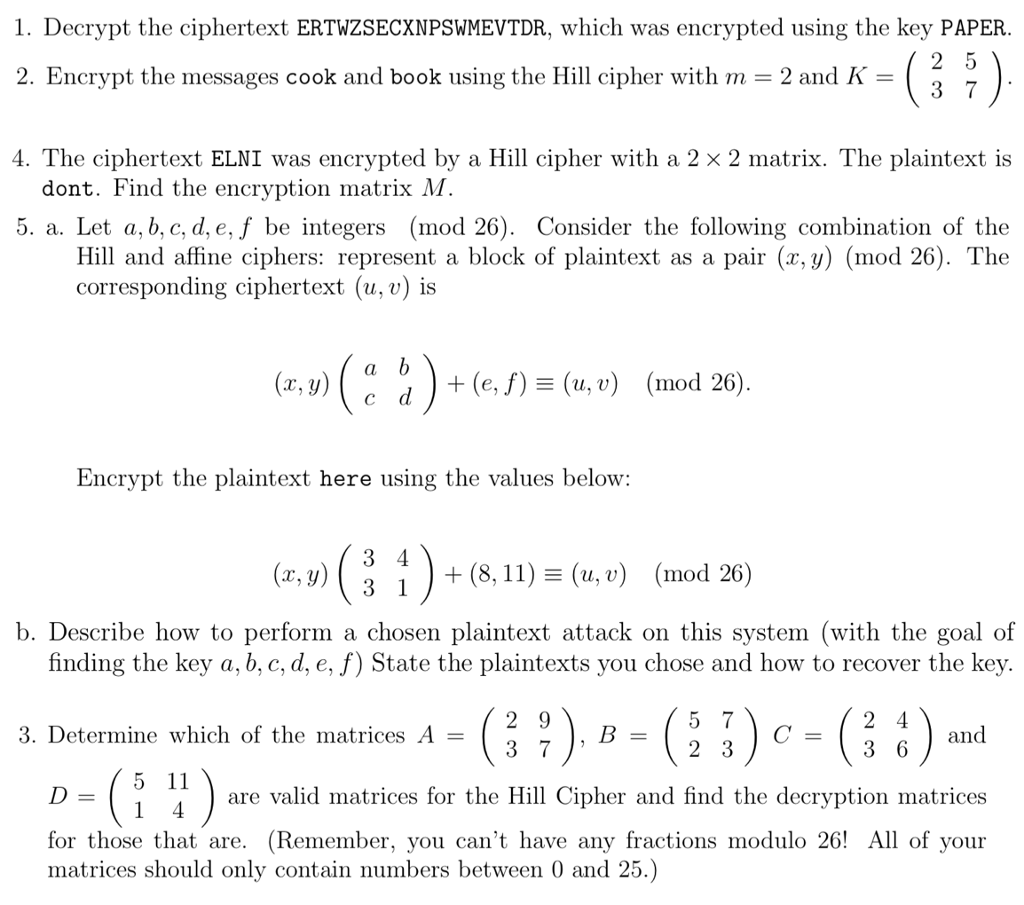
1. Decrypt the ciphertext ERTWZSECXNPSWMEVTDR, which was encrypted using the key PAPER 2. Encrypt the messages cook and book using the Hill cipher with m -2 and K - 4. The ciphertext ELNI was encrypted by a Hill cipher with a 2 2 matrix. The plaintext is dont. Find the encryption matrix M. 5. a. Let a, b, c, d, e, f be integers (mod 26). Consider the following combination of the Hill and affine ciphers: represent a block of plaintext as a pair (x,y) (mod 26). The corresponding ciphertext (u,v) is (x.u) dd )+(e,f)(u,") (mod 26) Encrvpt the plaintext here using the values below: (z, y)( i ) + (8, 11) (u, v) (mod 201 b. Describe how to perform a chosen plaintext attack on this system (with the goal of finding the key a, b, c, d, e, f) State the plaintexts you chose and how to recover the key 3, Determine which of the matrices A and 5 11 are valid matrices for the Hill Cipher and find the decryption matrices for those that are. (Remember, you can't have any fractions modulo 26! All of your matrices should only contain numbers between 0 and 1. Decrypt the ciphertext ERTWZSECXNPSWMEVTDR, which was encrypted using the key PAPER 2. Encrypt the messages cook and book using the Hill cipher with m -2 and K - 4. The ciphertext ELNI was encrypted by a Hill cipher with a 2 2 matrix. The plaintext is dont. Find the encryption matrix M. 5. a. Let a, b, c, d, e, f be integers (mod 26). Consider the following combination of the Hill and affine ciphers: represent a block of plaintext as a pair (x,y) (mod 26). The corresponding ciphertext (u,v) is (x.u) dd )+(e,f)(u,") (mod 26) Encrvpt the plaintext here using the values below: (z, y)( i ) + (8, 11) (u, v) (mod 201 b. Describe how to perform a chosen plaintext attack on this system (with the goal of finding the key a, b, c, d, e, f) State the plaintexts you chose and how to recover the key 3, Determine which of the matrices A and 5 11 are valid matrices for the Hill Cipher and find the decryption matrices for those that are. (Remember, you can't have any fractions modulo 26! All of your matrices should only contain numbers between 0 and
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started