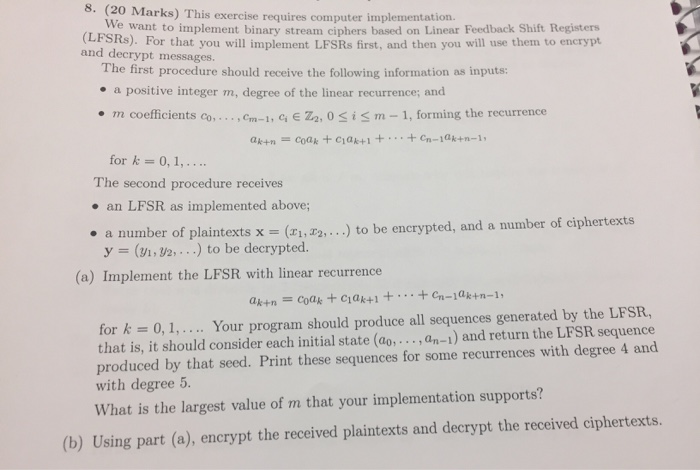
20 Marks) This exercise requires computer implementation. e want to implement binary stream ciphers based on Linear Feedback Shift Registers LFSRs)For that you will implement LFSRs first, and then you will use them to encryp and decrypt messages. The first procedure should receive the following information as inputs: . a positive integer m, degree of the linear recurrence; and m coefficients co,., om-1, c, E Z2, 0 SiSm -1, forming the recurrence for k 0, 1,.. The second procedure receives an LFSR as implemented above; to be encrypted, and a number of ciphertexts a number of plaintexts x (r1,. y ( 2...) to be decrypted. (a) Implement the LFSR with linear recurrence for k = 0, 1,, . .. Your program should produce all sequences generated by the LFSR, that is, it should consider each initial state (ao,..., an-1) and return the LFSR sequence produced by that seed. Print these sequences for some recurrences with degree 4 and with degree 5. What is the largest value of m that your implementation supports? (b) Using part (a), encrypt the received plaintexts and decrypt the received ciphertexts. 20 Marks) This exercise requires computer implementation. e want to implement binary stream ciphers based on Linear Feedback Shift Registers LFSRs)For that you will implement LFSRs first, and then you will use them to encryp and decrypt messages. The first procedure should receive the following information as inputs: . a positive integer m, degree of the linear recurrence; and m coefficients co,., om-1, c, E Z2, 0 SiSm -1, forming the recurrence for k 0, 1,.. The second procedure receives an LFSR as implemented above; to be encrypted, and a number of ciphertexts a number of plaintexts x (r1,. y ( 2...) to be decrypted. (a) Implement the LFSR with linear recurrence for k = 0, 1,, . .. Your program should produce all sequences generated by the LFSR, that is, it should consider each initial state (ao,..., an-1) and return the LFSR sequence produced by that seed. Print these sequences for some recurrences with degree 4 and with degree 5. What is the largest value of m that your implementation supports? (b) Using part (a), encrypt the received plaintexts and decrypt the received ciphertexts