Answered step by step
Verified Expert Solution
Question
1 Approved Answer
39)? Downloads Cryptography%20and%20Network%20Security%20 Forouzan%20 %20Copy.pdf%20%20PDF 737/121 ..etwork Security Forouzan -Co file / C: Users ibrahie CED a. The multiplicative key is the i mod 12)th
39)?
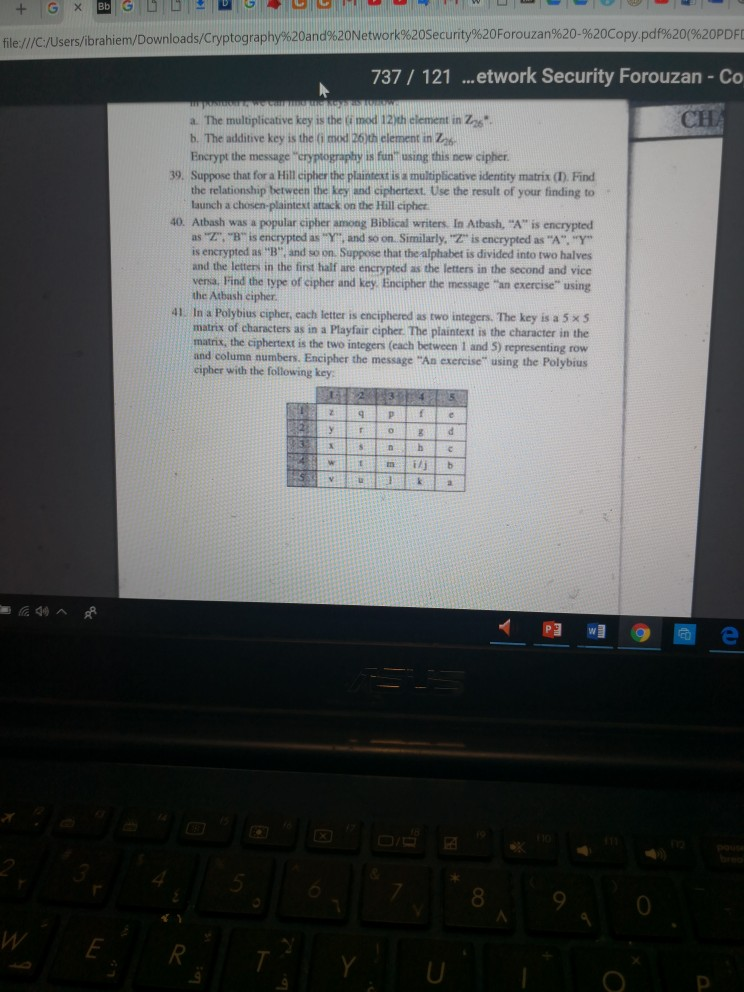
Downloads Cryptography%20and%20Network%20Security%20 Forouzan%20 %20Copy.pdf%20%20PDF 737/121 ..etwork Security Forouzan -Co file / C: Users ibrahie CED a. The multiplicative key is the i mod 12)th clement in Zzs b. The additive key is the (i mod 26)th element in Zab Encrypt the message "erypiography is fun using this new cipher 39. Suppose that for a Hill cipher the plaintext is a multiplicative identity matrix (). Find the relationship between the key and ciphertext. Use the result of your finding to launch a chosen-plaintext attack on the Hill cipher Atbash was a popular cipher among Biblical writers In Atbash, "A" is encrypted as "Z", "B" is encrypted as "Y", and so on. Similarly, "Z is encrypted as "A"."Y is encrypted as "B" and so on Suppose that the alphabet is divided into two and the letters in the first half are encrypted as the letters in the second and vice vensa. Find the type of cipher and key, Encipher the message "an exercise" using the Atbash cipher 40. 41. In a Polybius cipher, each letter is enciphered as two integers. The key is a 5 x s matrix of characters as in a Playfair cipher. The plaintext is the character in the matrix, the ciphertext is the two integers (each between 1 and 5) representing row and column numbers. Encipher cipher with the following key the message "An exercise" using the Polybius 4Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started