Question: 6 . 8 . Suppose F is a secure P R F with input length in , but we want to use it to construct
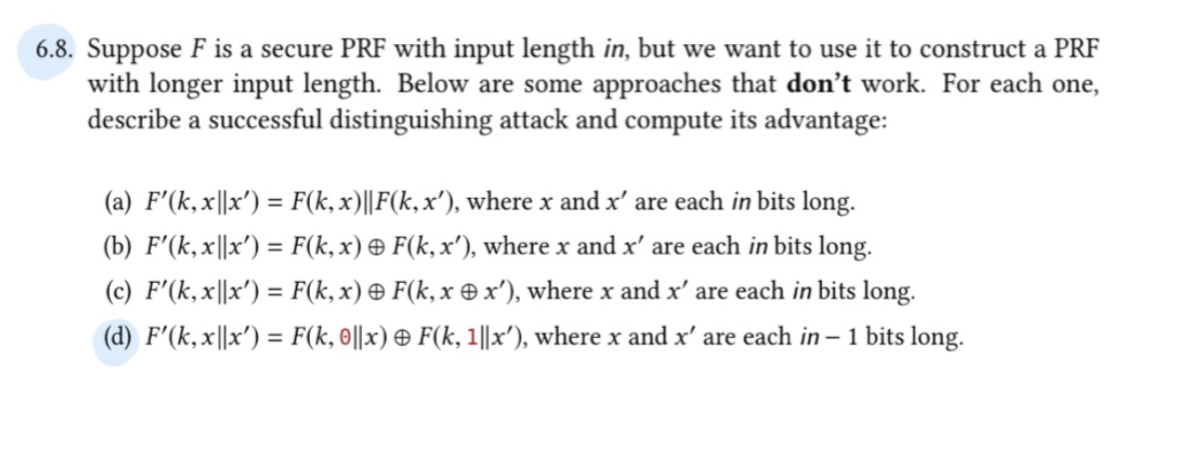
Suppose is a secure with input length in but we want to use it to construct a PRF
with longer input length. Below are some approaches that don't work. For each one,
describe a successful distinguishing attack and compute its advantage:
a where and are each in bits long.
b where and are each in bits long.
c where and are each in bits long.
d where and are each in bits long.
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


