Question
6. We consider the security services (A) confidentiality, (B) integrity, (C) authenticity, and (D) nonrepudiation, for a variety of simple protocols. The input is always
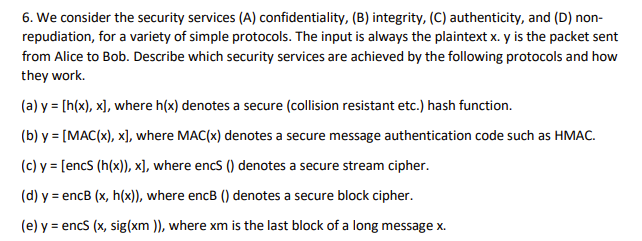 6. We consider the security services (A) confidentiality, (B) integrity, (C) authenticity, and (D) nonrepudiation, for a variety of simple protocols. The input is always the plaintext x. y is the packet sent from Alice to Bob. Describe which security services are achieved by the following protocols and how they work. (a) y = [h(x), x], where h(x) denotes a secure (collision resistant etc.) hash function. (b) y = [MAC(x), x], where MAC(x) denotes a secure message authentication code such as HMAC. (c) y = [encS (h(x)), x], where encS () denotes a secure stream cipher. (d) y = encB (x, h(x)), where encB () denotes a secure block cipher. (e) y = encS (x, sig(xm )), where xm is the last block of a long message x
6. We consider the security services (A) confidentiality, (B) integrity, (C) authenticity, and (D) nonrepudiation, for a variety of simple protocols. The input is always the plaintext x. y is the packet sent from Alice to Bob. Describe which security services are achieved by the following protocols and how they work. (a) y = [h(x), x], where h(x) denotes a secure (collision resistant etc.) hash function. (b) y = [MAC(x), x], where MAC(x) denotes a secure message authentication code such as HMAC. (c) y = [encS (h(x)), x], where encS () denotes a secure stream cipher. (d) y = encB (x, h(x)), where encB () denotes a secure block cipher. (e) y = encS (x, sig(xm )), where xm is the last block of a long message x
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started