Answered step by step
Verified Expert Solution
Question
1 Approved Answer
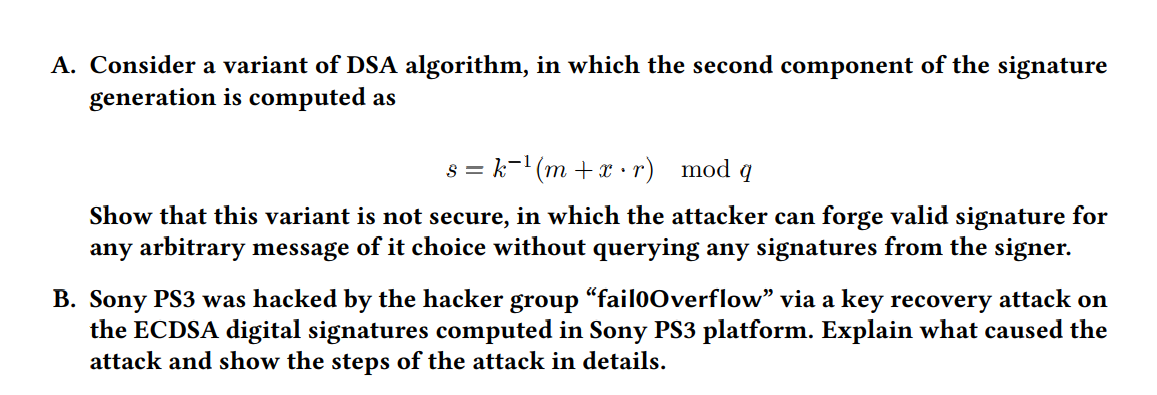
A . Consider a variant of DSA algorithm, in which the second component of the signature generation is computed as s = k - 1
A Consider a variant of DSA algorithm, in which the second component of the signature
generation is computed as
Show that this variant is not secure in which the attacker can forge valid signature for
any arbitrary message of it choice without querying any signatures from the signer.
B Sony PS was hacked by the hacker group "failOverflow" via a key recovery attack on
the ECDSA digital signatures computed in Sony PS platform. Explain what caused the
attack and show the steps of the attack in details.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started