Answered step by step
Verified Expert Solution
Question
1 Approved Answer
(a) In the firewall configuration shown below, assign appropriate security levels to parts of the configuration labeled A, B, and C. For this question,
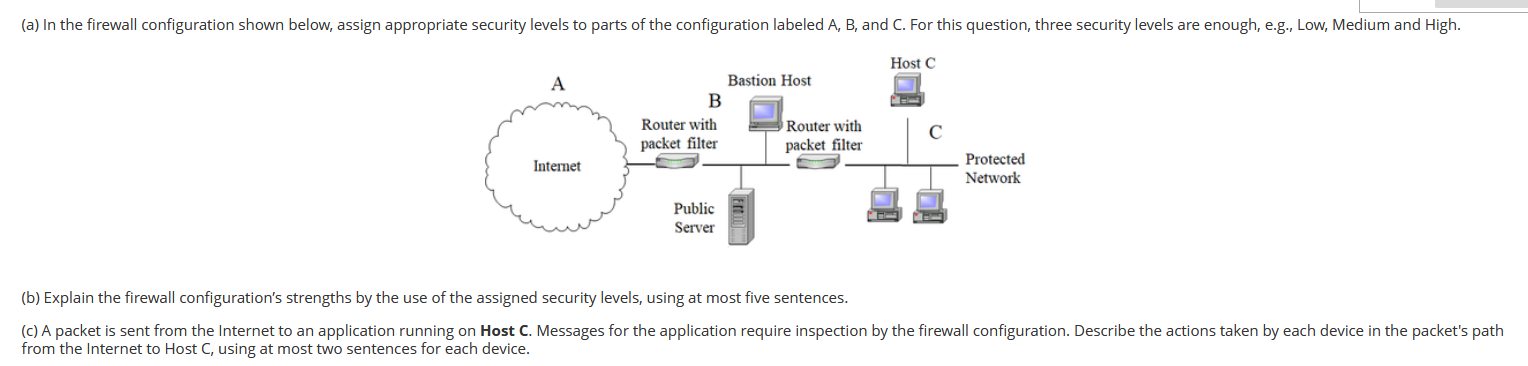
(a) In the firewall configuration shown below, assign appropriate security levels to parts of the configuration labeled A, B, and C. For this question, three security levels are enough, e.g., Low, Medium and High. Host C A Bastion Host B Router with packet filter Router with packet filter C Internet Protected Network Public Server (b) Explain the firewall configuration's strengths by the use of the assigned security levels, using at most five sentences. (c) A packet is sent from the Internet to an application running on Host C. Messages for the application require inspection by the firewall configuration. Describe the actions taken by each device in the packet's path from the Internet to Host C, using at most two sentences for each device.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


