Answered step by step
Verified Expert Solution
Question
1 Approved Answer
After examining the sequence diagram, explain three notation mistakes present in the diagram. These should only relate to the notation, do not discuss security weaknesses.
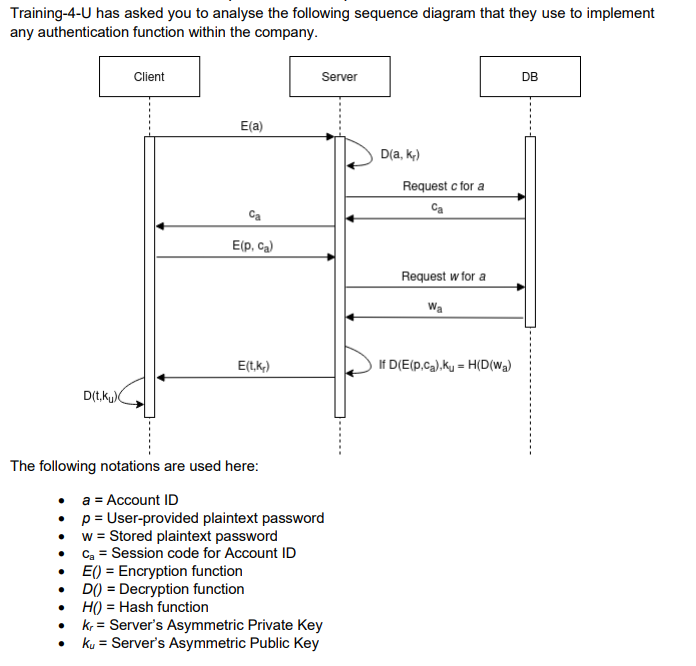
After examining the sequence diagram, explain three notation mistakes present in the diagram. These should only relate to the notation, do not discuss security weaknesses.
Training-4-U has asked you to analyse the following sequence diagram that they use to implement any authentiration f fnction within the romnan ] The followviny invauvi io alo noou inoro. - a= Account ID - p= User-provided plaintext password - w= Stored plaintext password - ca= Session code for Account ID - E()= Encryption function - D()= Decryption function - H()= Hash function - kr= Server's Asymmetric Private Key - ku= Server's Asymmetric Public KeyStep by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


