Answered step by step
Verified Expert Solution
Question
1 Approved Answer
ald months, he has been designing a system of controls to allow and restrict access to network assets based on various method's and information. He
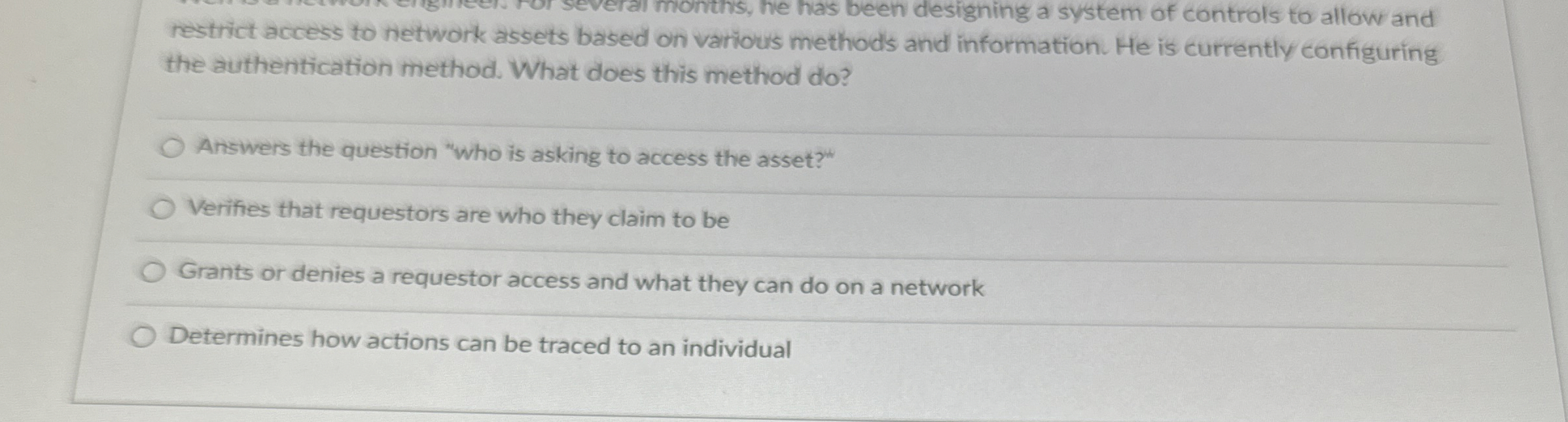
ald months, he has been designing a system of controls to allow and restrict access to network assets based on various method's and information. He is currently configuring the authentication method. What does this method do
Answers the question "who is asking to access the asset?"
Verifies that requestors are who they claim to be
Grants or denies a requestor access and what they can do on a network
Determines how actions can be traced to an individual
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


