Answered step by step
Verified Expert Solution
Question
1 Approved Answer
can I get help with this please Q1: If the key K is stored in an unencrypted text file in the same directory where F
can I get help with this please
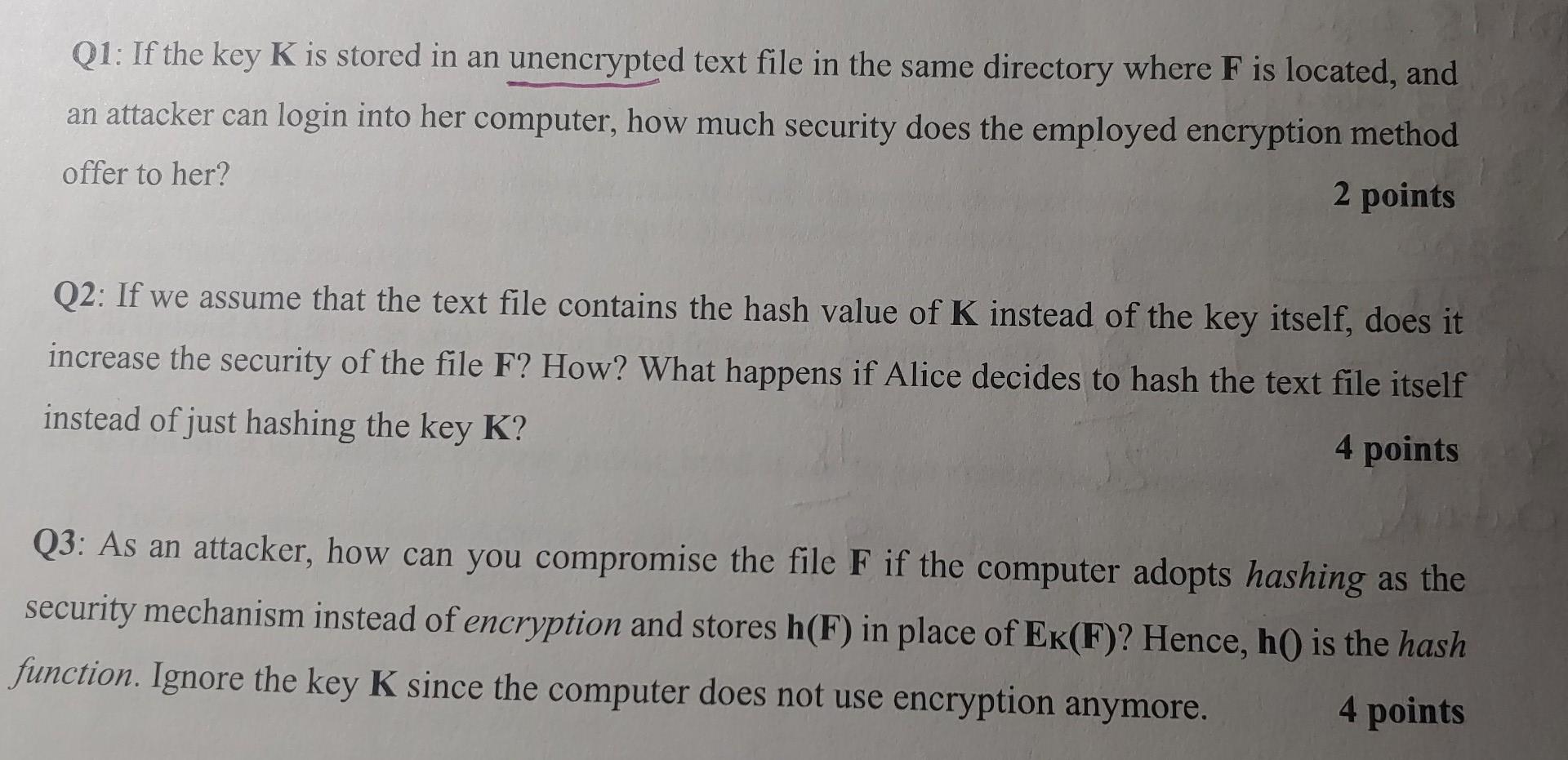
Q1: If the key K is stored in an unencrypted text file in the same directory where F is located, and an attacker can login into her computer, how much security does the employed encryption method offer to her? 2 points Q2: If we assume that the text file contains the hash value of K instead of the key itself, does it increase the security of the file F? How? What happens if Alice decides to hash the text file itself instead of just hashing the key K? 4 points Q3: As an attacker, how can you compromise the file F if the computer adopts hashing as the security mechanism instead of encryption and stores h(F) in place of Ek(F)? Hence, h() is the hash function. Ignore the key K since the computer does not use encryption anymore. 4 points
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started