Answered step by step
Verified Expert Solution
Question
1 Approved Answer
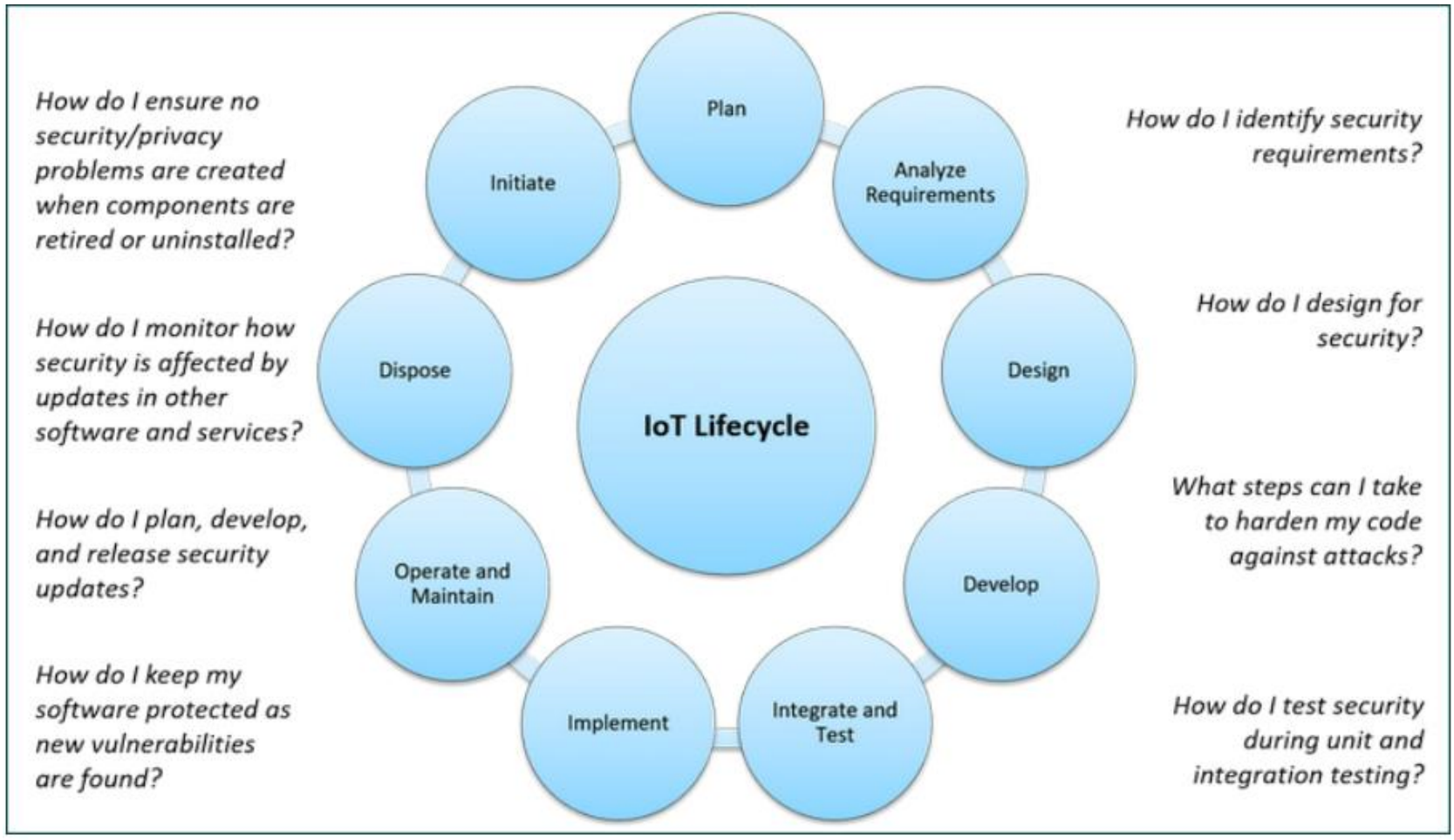
Cyber Security Throughout the IoT Life Cycle. These are examples, can you do in the same way please, thank you 1 . Identifying Security Requirements
Cyber Security Throughout the IoT Life Cycle. These are examples, can you do in the same way please, thank you Identifying Security Requirements
Example: Smart Door Lock System
Process: Conducting a risk assessment for a smart door lock system.
Result: Identifying security requirements such as encryption for data
transmission, multifactor authentication for user access, regular firmware
updates, and secure storage of user credentials.
Designing for Security
Example: Smart Thermostat Design
Approach: Designing a smart thermostat with security as a primary
consideration.
Implementation: Utilizing secure communication protocols like MQTT or
HTTPS for data exchange, implementing device authentication, and designing
with tamperresistant hardware.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started