Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Diffie - Hellman ( 2 - 2 - 2 - 6 ) Consider a Diffie - Hellman key exchange with p = 1 3 and
DiffieHellman Consider a DiffieHellman key exchange with and a Alice picks what is the public key A will send to Bob? b Bob picks what is the public he will send to Alice? c What is the shared key resulting from the exchange? d One weakness of is that it is vulnerable to ManintheMiddle attack. How could you modify the exchanged messages in DH to prevent this attack? Clearly state all your assumptions including any additional cryptographic algorithm or material needed and the notation you used. 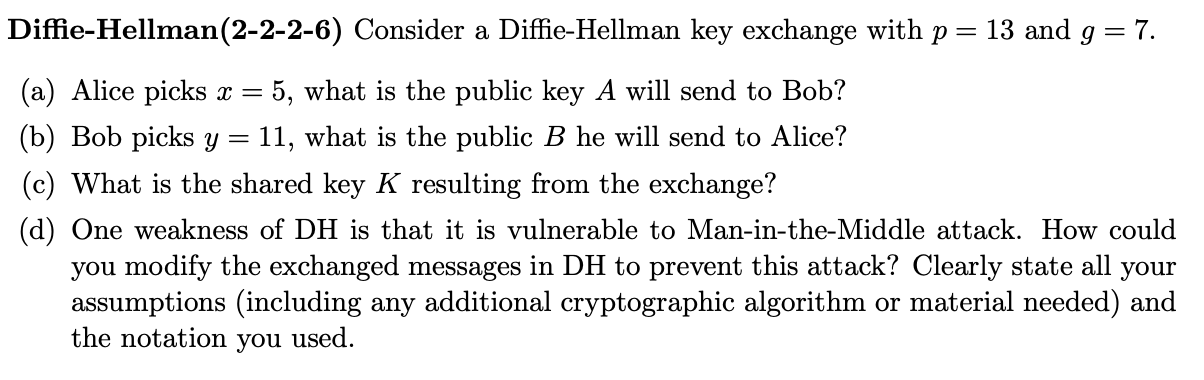
DiffieHellman Consider a DiffieHellman key exchange with and
a Alice picks what is the public key A will send to Bob?
b Bob picks what is the public he will send to Alice?
c What is the shared key resulting from the exchange?
d One weakness of is that it is vulnerable to ManintheMiddle attack. How could
you modify the exchanged messages in DH to prevent this attack? Clearly state all your assumptions including any additional cryptographic algorithm or material needed and the notation you used.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started