Answered step by step
Verified Expert Solution
Question
1 Approved Answer
In this lab, we will start basic configuration and routing, then we will evaluate the use of access lists in Routers. Start by creating the
In this lab, we will start basic configuration and routing, then we will evaluate the use of access lists in Routers. Start by creating the topology below:
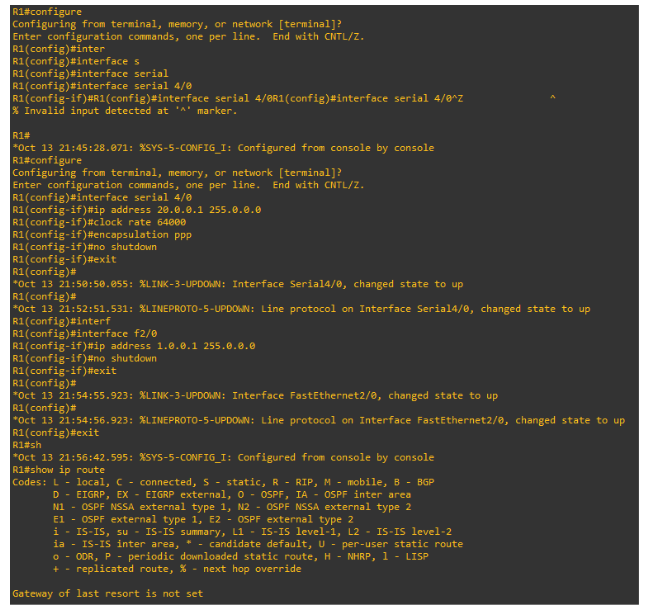
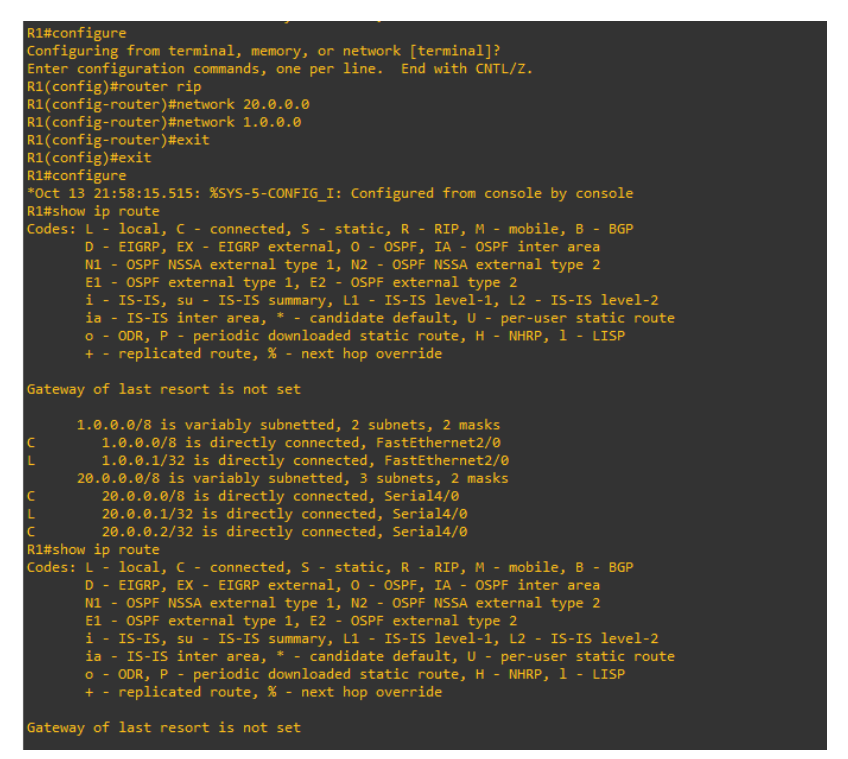
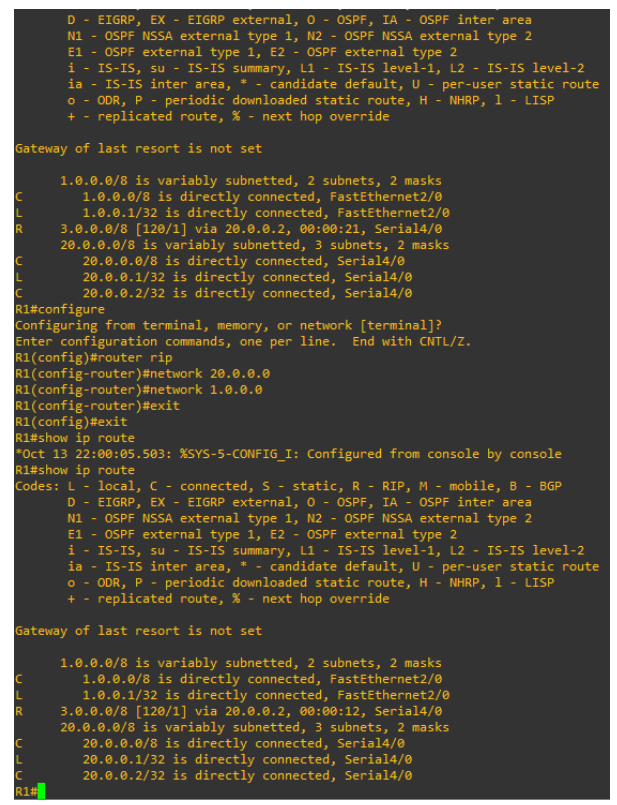
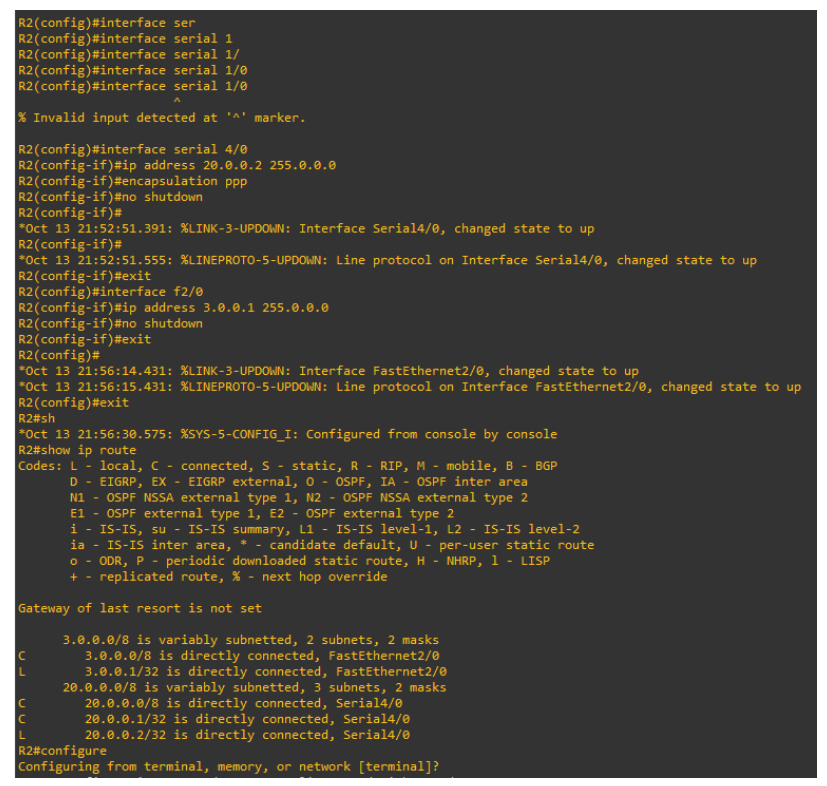
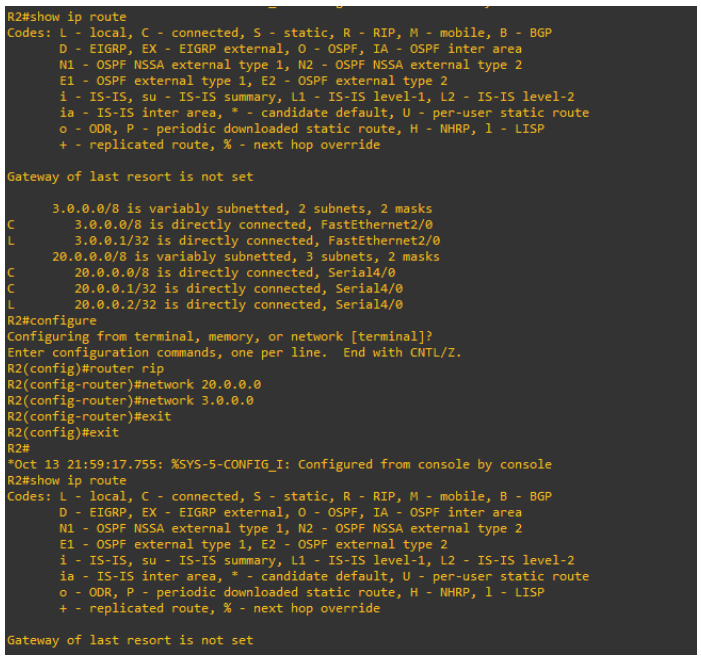
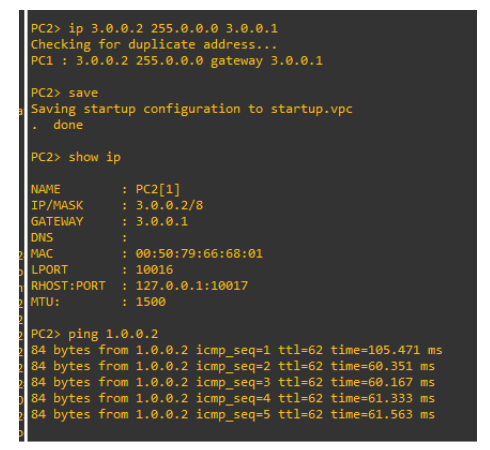
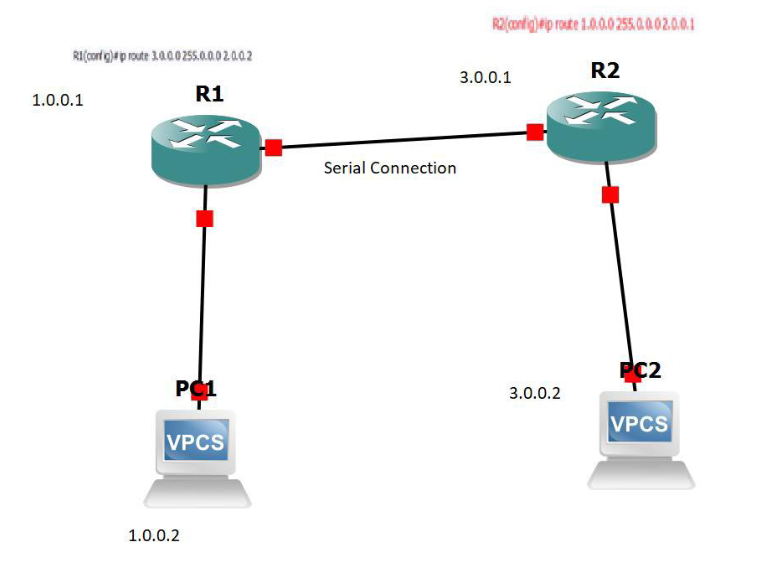 Step 1: Configure IP Address on routers. R1-Configuration
Step 1: Configure IP Address on routers. R1-Configuration
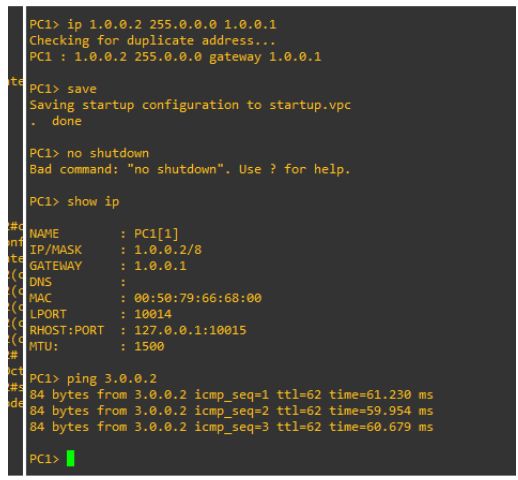
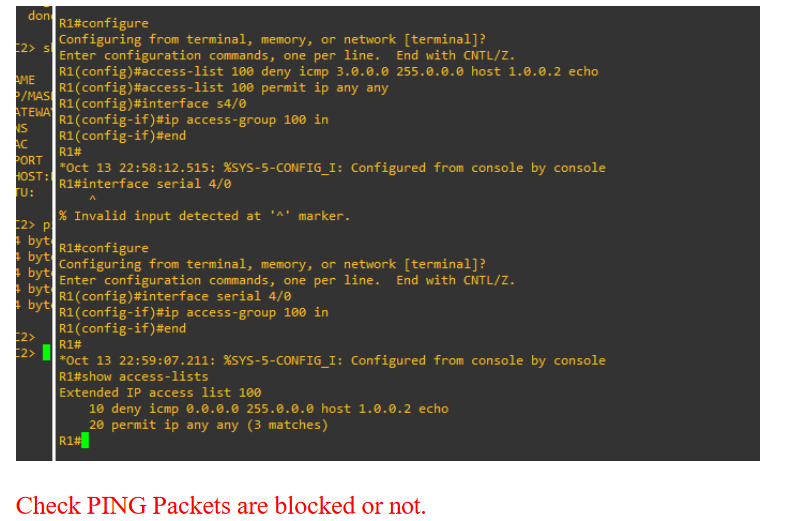
Access List Configuration Now Configure Extended ACL on router R1 so that it will block ping packets but allow others.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started