Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Is the part a only Cathy? also provide correct answers for all parts and detailed explanation 10. (10 pts) The following table shows the access
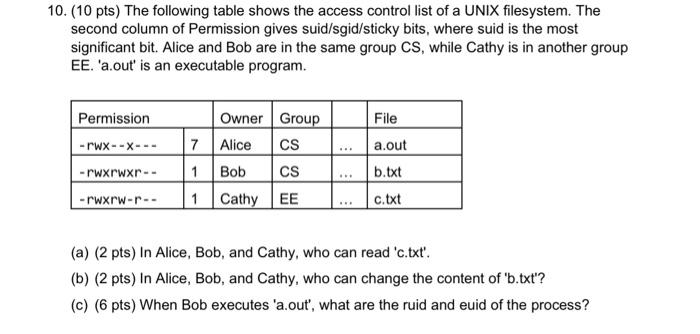
Is the part a only Cathy?also provide correct answers for all parts and detailed explanation 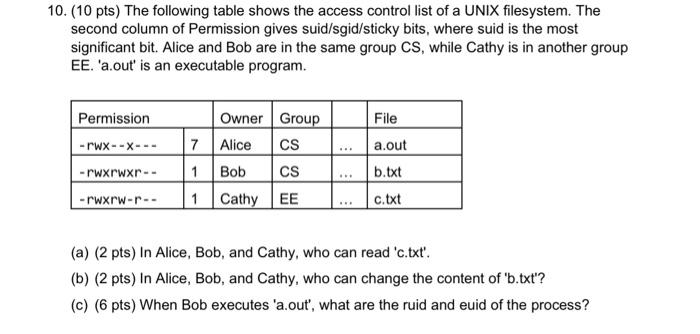 10. (10 pts) The following table shows the access control list of a UNIX filesystem. The second column of Permission gives suid/sgid/sticky bits, where suid is the most significant bit. Alice and Bob are in the same group CS, while Cathy is in another group EE. 'a.out' is an executable program. (a) (2 pts) In Alice, Bob, and Cathy, who can read 'c.txt'. (b) (2 pts) In Alice, Bob, and Cathy, who can change the content of 'b.txt'? (c) (6 pts) When Bob executes 'a.out', what are the ruid and euid of the process
10. (10 pts) The following table shows the access control list of a UNIX filesystem. The second column of Permission gives suid/sgid/sticky bits, where suid is the most significant bit. Alice and Bob are in the same group CS, while Cathy is in another group EE. 'a.out' is an executable program. (a) (2 pts) In Alice, Bob, and Cathy, who can read 'c.txt'. (b) (2 pts) In Alice, Bob, and Cathy, who can change the content of 'b.txt'? (c) (6 pts) When Bob executes 'a.out', what are the ruid and euid of the process
also provide correct answers for all parts
and detailed explanation 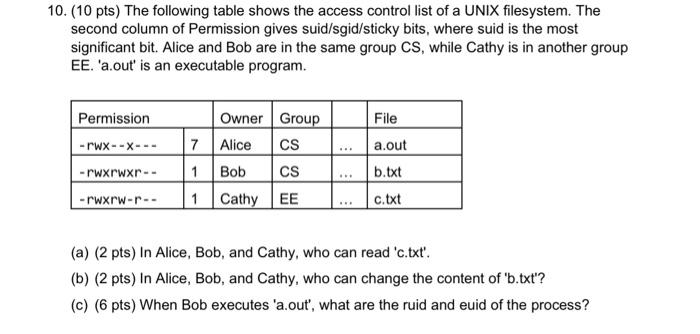
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started