Answered step by step
Verified Expert Solution
Question
1 Approved Answer
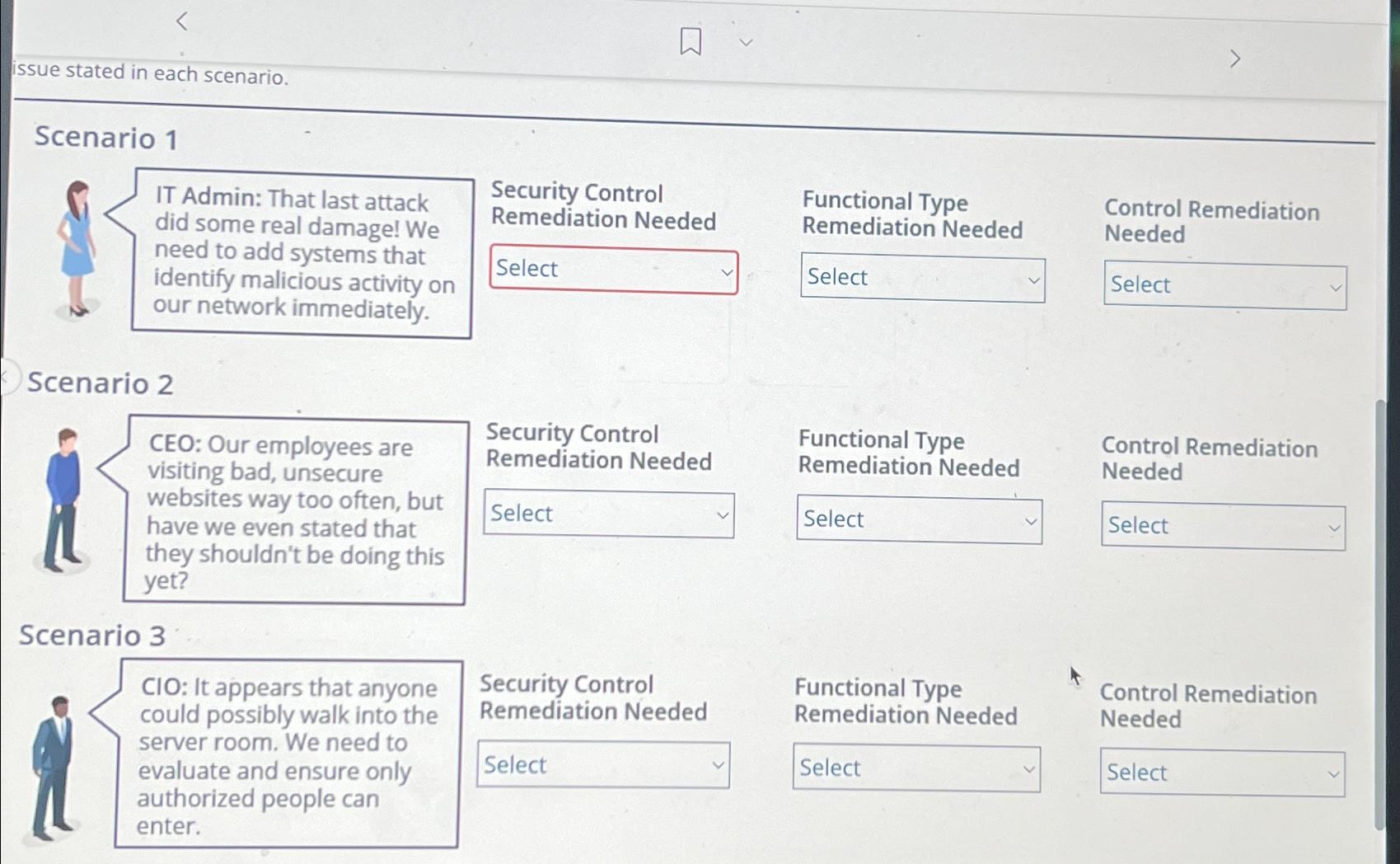
issue stated in each scenario. Scenario 1 IT Admin: That last attack did some real damage! We need to add systems that identify malicious activity
issue stated in each scenario.
Scenario
IT Admin: That last attack did some real damage! We need to add systems that identify malicious activity on our network immediately.
Security Control Remediation Needed
Functional Type
Remediation Needed
Control Remediation Needed
Functional Type Remediation Needed
Functional Type
Remediation Needed
Control Remediation Needed
Scenario
CEO: Our employees are visiting bad, unsecure websites way too often, but have we even stated that they shouldn't be doing this yet?
Scenario
CIO : It appears that anyone could possibly walk into the server room. We need to evaluate and ensure only authorized people can enter.
Security Control Remediation Needed
Control Remediation Needed
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


