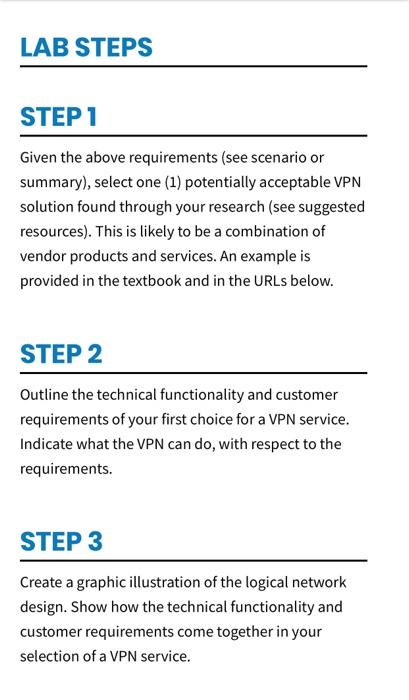
LAB OVERVIEW SCENARIO/SUMMARY In this lab, you will explore, select, and justify the selection of a virtual private network (VPN) for a midsize network. You shall actually identify the hardware and software needed to meet the network security and users requirements. The reason for this lab is to allow you to experience the VPN technology selection process, while working with a limited set of requirements and the current industry offerings. Basic VPN requirements and assumptions are as follows. Basic VPN requirements and assumptions are as follows. Access control to the VPN is based on a user ID and password 120 simultaneous VPN connections must be supported. User (client) connection speeds range from 3 to 30 megabits. No, or minimal, client software setup is required. No special hardware is required by the client system. Full data encryption for all network traffic is required. Protection against man-in-the- middle attacks is required. Remote administration (includes reconfiguration) to the VPN is required. Access control and right or permissions are integrated into other services, such as active directory for Windows configurations. Access (read or write) to network resources, such as file shares (virtual drives), web servers, database servers, and so forth is required. Assume users will be using a Windows, MAC, and Linux client system released within the last 3 years. Assume a web browser will be used to access the web servers. Assume the client will have preinstalled applications that can access file shares and database servers. Assume the host firewall will support your selection. . The selected vendor(s) must have an excellent reputation for quality and support. Cloud-based, non-cloud-based, and hybrid solutions are all acceptable. DELIVERABLES DOCUMENT AUTHORING GUIDELINES Each section will vary in size based on the requirements. Drive yourself to create a useful document for the direction you have selected. LAB DOCUMENT FRAMEWORK Potentially Acceptable VPN Solution: State the general characteristics of one solution that meets the security and user requirements. Name the vendor(s) and VPN services. It is generally about 3 sentences. VPN Solution Overview: Outline the technical functionality and customer requirements of your first choice for a VPN service. This may take the form of a feature chart that is mapped to the requirements. Include any special conditions, limitations, or exceptions that exist. It is generally about 2 pages. Network Design Illustration: Using a graphic illustration tool, such as Visio, document the logical design of your VPN solution. It is generally about 2 pages. Citations and Resources Used in this Report: Tell us where you received external guidance and ideas. If you have presented original ideas, then give yourself credit and tell us why you believe it is correct. LAB STEPS STEP 1 1 Given the above requirements (see scenario or summary), select one (1) potentially acceptable VPN solution found through your research (see suggested resources). This is likely to be a combination of vendor products and services. An example is provided in the textbook and in the URLs below. STEP 2 Outline the technical functionality and customer requirements of your first choice for a VPN service. Indicate what the VPN can do, with respect to the requirements. STEP 3 Create a graphic illustration of the logical network design. Show how the technical functionality and customer requirements come together in your selection of a VPN service