Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Message to convert is Security (a) We can use Radix-64 code as encryption method (there is no key). Assuming the attacker does not know the
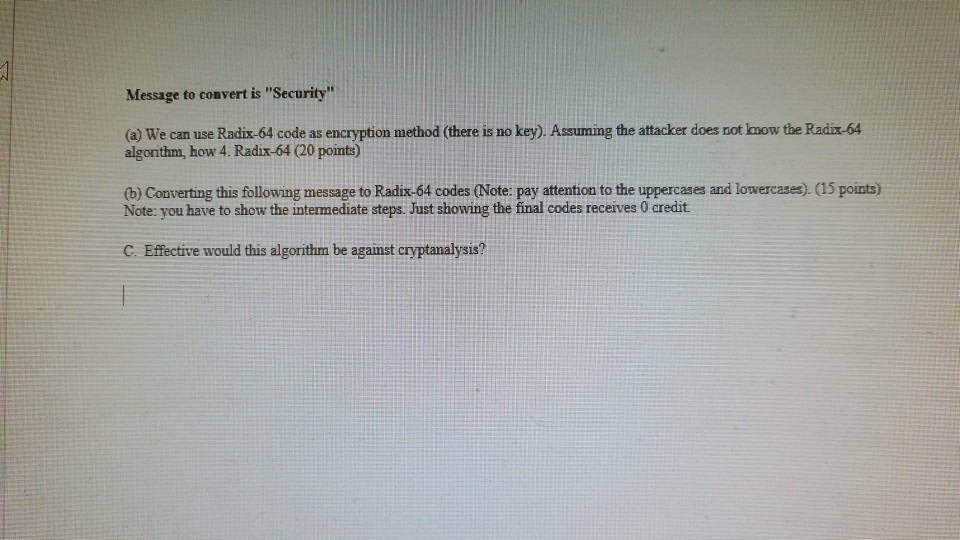
Message to convert is "Security" (a) We can use Radix-64 code as encryption method (there is no key). Assuming the attacker does not know the Radix-64 algorithm, how 4. Radix-64 (20 points) (b) Converting this following message to Radix-64 codes (Note: pay attention to the uppercases and lowercases). (15 points) Note: you have to show the intermediate steps. Just showing the final codes receives 0 credit C. Effective would this algorithm be against cryptanalysis
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started