Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Please if you are not sure from your answer 100% do not answer this s question. Thanks in advance A cybersecurity analyst is performing a
Please if you are not sure from your answer 100% do not answer this s question. Thanks in advance 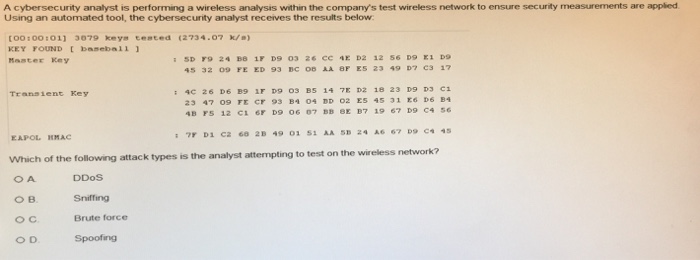
A cybersecurity analyst is performing a wireless analysis within the company's test wireless network to ensure security measurements are appled Using an automated tool, the cybersecurity analyst receives the results below [o0:00:011 3079 keya cested (2734.07) KEY FOUND basebail Master Key 5 32 09 FE ED 93 BC 08 AA 8F ES 23 49 D7 e3 17 Transient Key 23 47 09 FE CF 93 B4 04 DD 02 ES 45 31 E6 D6 B4 EAPOL HMAC Which of the following attack types is the analyst attempting to test on the wir DDoS Sniffing Brute force Spoofing . O D 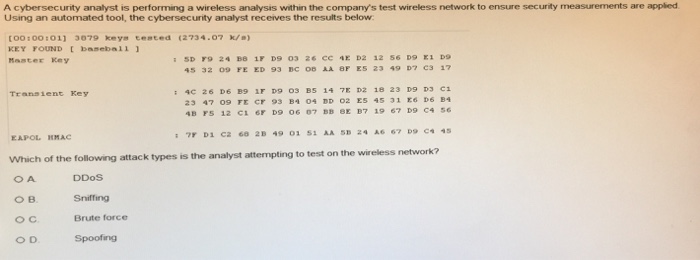
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


