Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Polynomial Functions Cryptology is the study of making and breaking secret codes. Secret codes are often used to send messages over the Internet. By devising
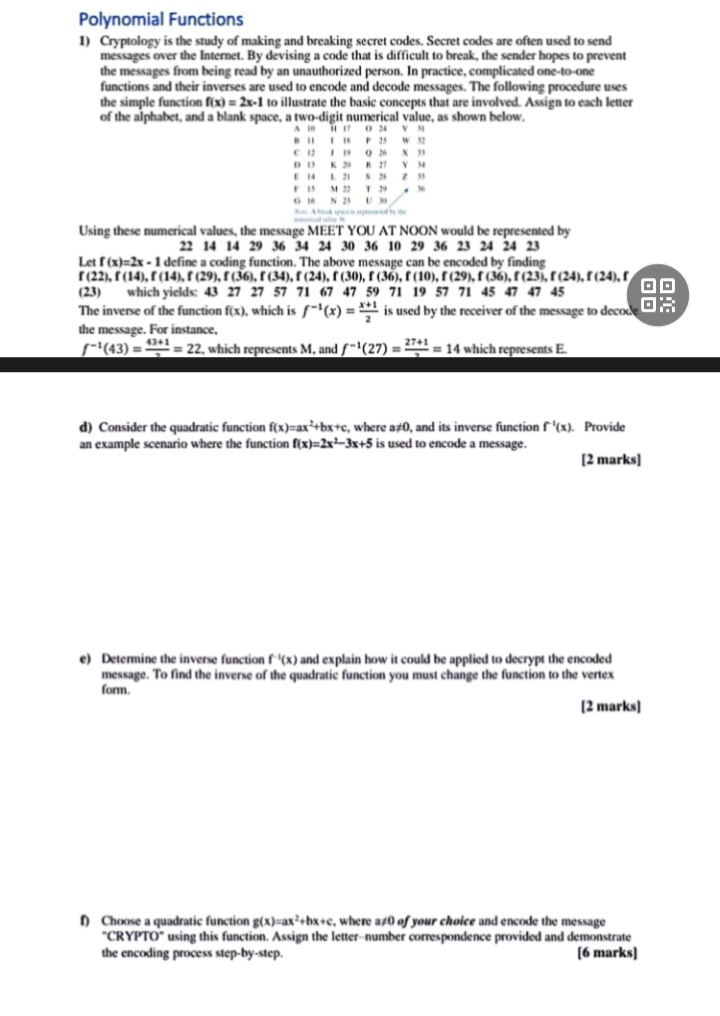
Polynomial Functions
Cryptology is the study of making and breaking secret codes. Secret codes are often used to send messages over the Internet. By devising a code that is difficult to break, the sender hopes to prevent the messages from being read by an unauthorized person. In practice, complicated onetoone functions and their inverses are used to encode and decode messages. The following procedure uses the simple function to illustrate the basic concepts that are involved. Assign to each letter of the alphabet, and a blank space, a twodigit numerical value, as shown below.
tableAis
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


