Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Problem 3 . ElGamal tricks. Bob's corporate mail server publishes a public - key p k b o b so that all incoming emails to
Problem ElGamal tricks. Bob's corporate mail server publishes a publickey so that all
incoming emails to Bob are encrypted under When Bob goes on vacation he instructs the
company's mail server to forward all his incoming email to his colleague Alice. Alice's public key
is The mail server needs a way to translate an email encrypted under publickey
into an email encrypted under publickey This would be easy if the mail server had sk
but then the mail server could read all of Bob's incoming email, which is undesirable.
Let be a group of prime order with generator ginG. Consider a minor variation of the
ElGamal encryption scheme from lecture where encryption using a public key pk :inG
works as follows:
klarrH output
Here is the encryption algorithm of a symmetric cipher with key space and is a
hash function :
Suppose that and are public keys for this scheme with corresponding secret keys
and To enable private translation of ciphertexts from to
Alice and Bob get together to compute : They give to the mail server.
a Explain how the mail server uses to translate a ciphertext to a ciphertext
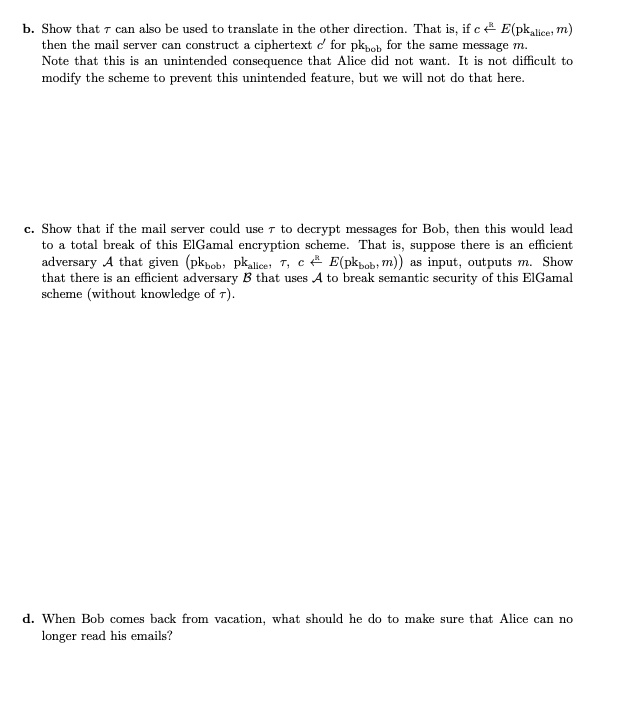
for for the same message Justify your answer.b Show that can also be used to translate in the other direction. That is if
then the mail server can construct a ciphertext for for the same message
Note that this is an unintended consequence that Alice did not want. It is not difficult to
modify the scheme to prevent this unintended feature, but we will not do that here.
c Show that if the mail server could use to decrypt messages for Bob, then this would lead
to a total break of this ElGamal encryption scheme. That is suppose there is an efficient
adversary A that given : as input, outputs Show
that there is an efficient adversary that uses to break semantic security of this ElGamal
scheme without knowledge of
d When Bob comes back from vacation, what should he do to make sure that Alice can no
longer read his emails?
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


