Answered step by step
Verified Expert Solution
Question
1 Approved Answer
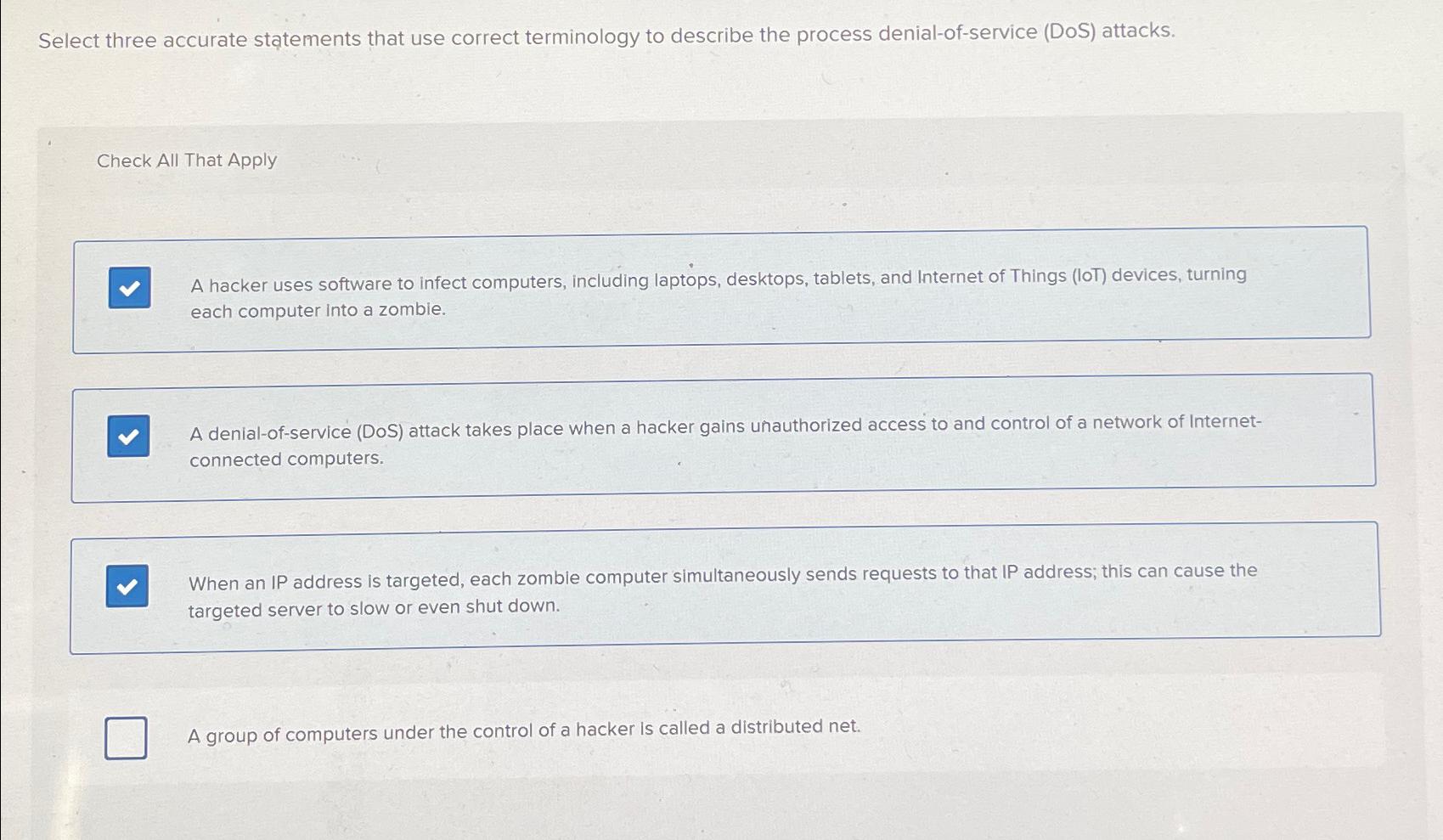
Select three accurate statements that use correct terminology to describe the process denial - of - service ( DoS ) attacks. Check All That Apply
Select three accurate statements that use correct terminology to describe the process denialofservice DoS attacks.
Check All That Apply
A hacker uses software to infect computers, including laptops, desktops, tablets, and Internet of Things IoT devices, turning each computer into a zombie.
A denialofservice DoS attack takes place when a hacker gains unauthorized access to and control of a network of Internetconnected computers.
When an IP address is targeted, each zomble computer simultaneously sends requests to that IP address; this can cause the targeted server to slow or even shut down.
A group of computers under the control of a hacker is called a distributed net.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


