Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Suggest potential security flaws for each of the arguments (URL's), as if this were a black-box and the back end code is unknown. The cart
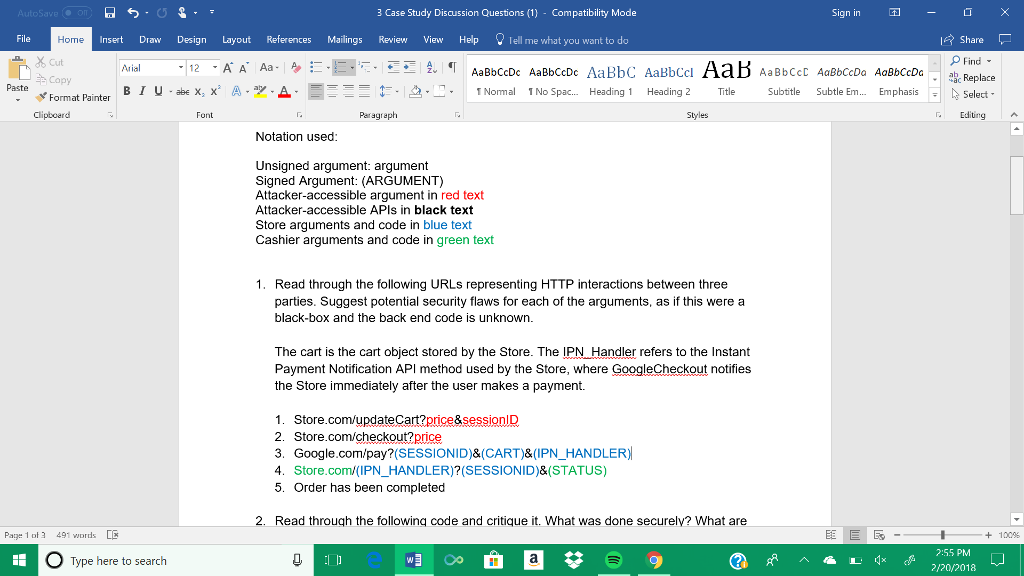
Suggest potential security flaws for each of the arguments (URL's), as if this were a black-box and the back end code is unknown.
The cart is the cart object stored by the Store. The IPN_Handler refers to the Instant Payment Notification API method used by the Store, where GoogleCheckout notifies the Store immediately after the user makes a payment.
3 Case Study Discussion Questions (1) - Compatibility Mode Sign in Insert Draw Design Layout References Mailings Review View Help Tell me what you want to do Home Cut copy I Share OFind Arial Paste Bluabex, x, A.2. --. :2. 'Normal 'NoSpac. Heading 1 Heading 2 Title Subtitle Subtle Em Emphasis Select Format Pair ter Clipboard Paragraph Styles Editing A Notation used Unsigned argument: argument Signed Argument: (ARGUMENT) Attacker-accessible argument in red text Attacker-accessible APls in black text Store arguments and code in blue text Cashier arguments and code in green text 1. Read through the following URLs representing HTTP interactions between three parties. Suggest potential security flaws for each of the arguments, as if this were a black-box and the back end code is unknown. The cart is the cart object stored by the Store. The IPN Handler refers to the Instant Payment Notification API method used by the Store, where GoogleCheckout notifies the Store immediately after the user makes a payment. 1. Store.com/updateCart?price&sessionlD 2. Store.com/checkout?price 3. Google.com/pay?(SESSIONID)&(CART)&(IPN HANDLER) 4. Store.com/(IPN_HANDLER)?(SESSIONID)&(STATUS) 5. Order has been completed 2. Read through the following code and critique it. What was done securely? What are Page 1 of 3 491 words + 100% 2:55 PM Type here to search 2/20/2018 3 Case Study Discussion Questions (1) - Compatibility Mode Sign in Insert Draw Design Layout References Mailings Review View Help Tell me what you want to do Home Cut copy I Share OFind Arial Paste Bluabex, x, A.2. --. :2. 'Normal 'NoSpac. Heading 1 Heading 2 Title Subtitle Subtle Em Emphasis Select Format Pair ter Clipboard Paragraph Styles Editing A Notation used Unsigned argument: argument Signed Argument: (ARGUMENT) Attacker-accessible argument in red text Attacker-accessible APls in black text Store arguments and code in blue text Cashier arguments and code in green text 1. Read through the following URLs representing HTTP interactions between three parties. Suggest potential security flaws for each of the arguments, as if this were a black-box and the back end code is unknown. The cart is the cart object stored by the Store. The IPN Handler refers to the Instant Payment Notification API method used by the Store, where GoogleCheckout notifies the Store immediately after the user makes a payment. 1. Store.com/updateCart?price&sessionlD 2. Store.com/checkout?price 3. Google.com/pay?(SESSIONID)&(CART)&(IPN HANDLER) 4. Store.com/(IPN_HANDLER)?(SESSIONID)&(STATUS) 5. Order has been completed 2. Read through the following code and critique it. What was done securely? What are Page 1 of 3 491 words + 100% 2:55 PM Type here to search 2/20/2018
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


