Answered step by step
Verified Expert Solution
Question
1 Approved Answer
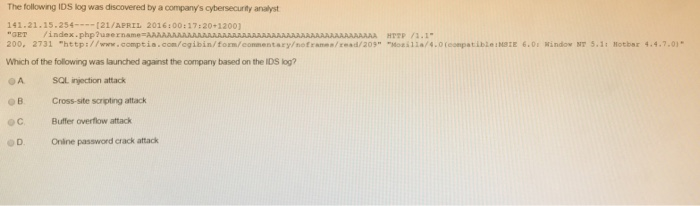
The following IDS log was discovered by a company's cybersecurity analyst 141-21.15-254--121/AFRIL 2016:00:17:20-1200) GET index.php?user 200. 2731 http://www .comptia.com/cgibin/fom/eommentaryotranns / read/20, Mozilla/.0(eonpatiblensze 6.01 Randowy7 5.1,
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started