Question: The following scenario is an example of privilege elevation; select the answer that implements the appropriate mitigation. Scenario: Credential Exploitation frequently allow access to sensitive
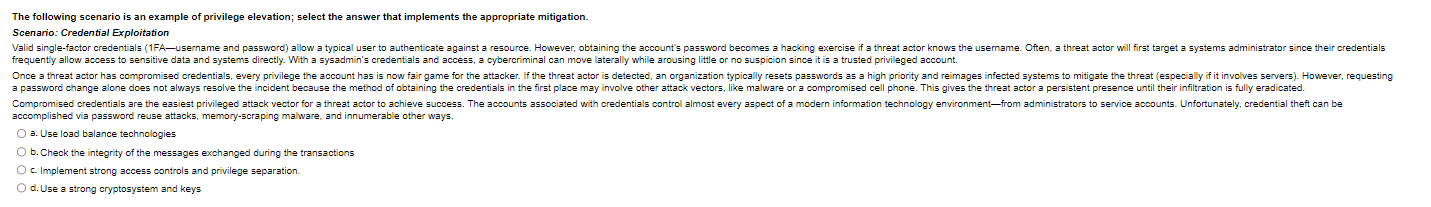
The following scenario is an example of privilege elevation; select the answer that implements the appropriate mitigation.
Scenario: Credential Exploitation
frequently allow access to sensitive data and systems directly. With a sysadmin's credentials and access, a cybercriminal can move laterally while arousing little or no suspicion since it is a trusted privileged account.
accomplished via password reuse attacks, memoryscraping malware, and innumerable other ways.
a Use load balance technologies
b Check the integrity of the messages exchanged during the transactions
c Implement strong access controls and privilege separation.
d Use a strong cryptosystem and keys
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


