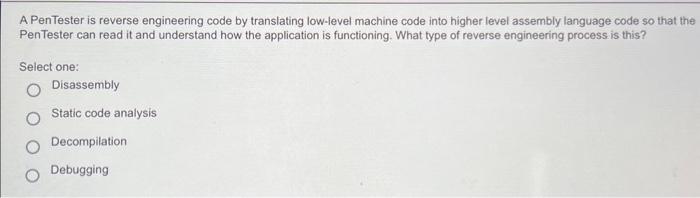
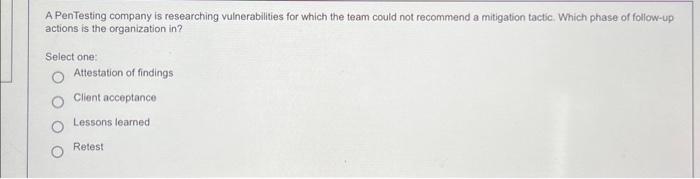
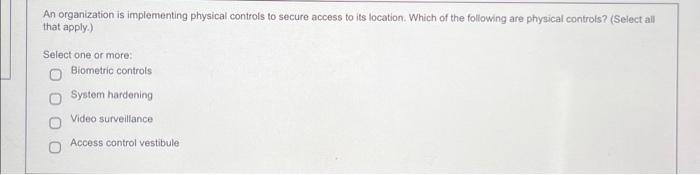
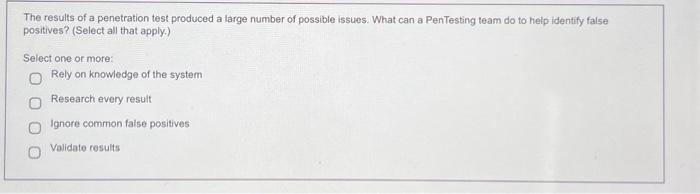
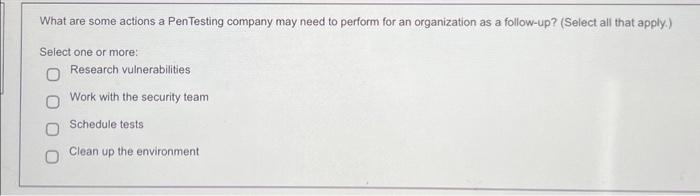
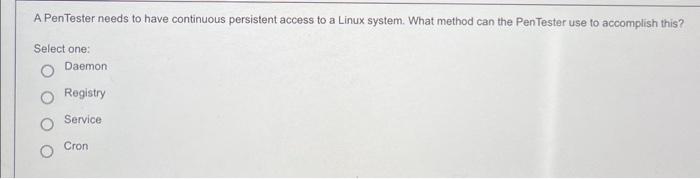
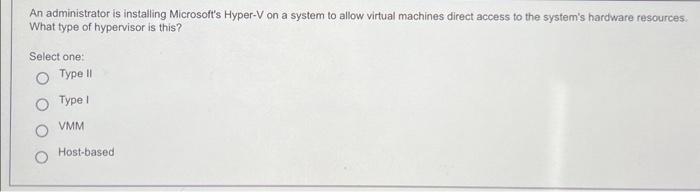
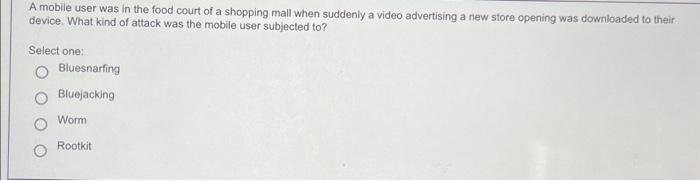
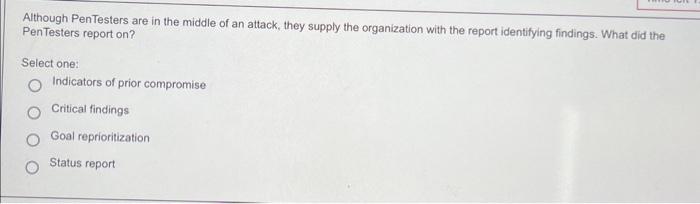
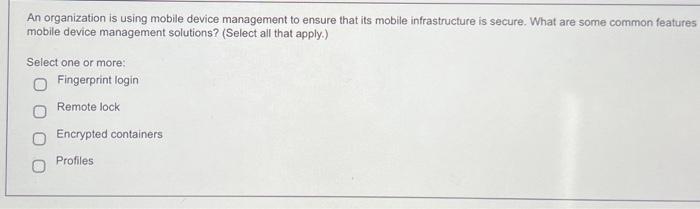
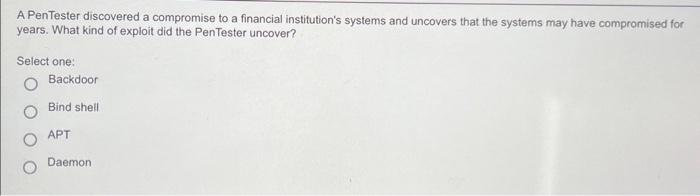
A PenTester is reverse engineering code by translating low-level machine code into higher level assembly language code so that the Pentester can read it and understand how the application is functioning. What type of reverse engineering process is this? Select one: Disassembly Static code analysis Decompilation Debugging A PenTesting company is researching vulnerabilities for which the team could not recommend a mitigation tactic. Which phase of follow-up actions is the organization in? Select one: Attestation of findings Client acceptance Lessons leamed Retest An organization is implementing physical controls to secure access to its location. Which of the following are physical controls? (Select all that apply.) Select one or more: Biometric controls System hardening Video surveillance Access control vestibule The results of a penetration test produced a large number of possible issues. What can a PenTesting team do to help identify false positives? (Select all that apply.) Select one or more: Rely on knowledge of the system Research every result Ignore common faise positives Validate results A penetration tester is using Netcat and does not want the command to perform DNS lookups for host names on the other end of the connection. What option will accomplish this? Select one: z n +1 op A PenTester is using a tool that allows the PenTester to pivot from one host to another exfiltrating files from each target to the PenTester's own host. What tool is the PenTester most likely using? Select one: Netcat RAT Registry Cron job The C-Suite is reviewing a report section that details the issues that PenTesters discovered during the most recent test and the altack vectors they successfully exploited. What section of the report is this? Select one: Scope Findings Attack narrative Executive summary A Pentesting team launched an attack against a system without using a rate-limit making the system nearly unusable. What can the team do to mitigate this issue? Select one: Consult legal counsel De-escalate Deconfict Goal reprioritization What are some actions a PenTesting company may need to perform for an organization as a follow-up? (Select all that apply.) Select one or more: Research vulnerabilities Work with the security team Schedule tests Clean up the environment A PenTester needs to have continuous persistent access to a Linux system. What method can the PenTester use to accomplish this? Select one: Daemon Registry Service Cron An administrator is installing Microsoft's Hyper-V on a system to allow virtual machines direct access to the system's hardware resources. What type of hypervisor is this? Select one: Type II Type I VMM Host-based A mobile user was in the food court of a shopping mall when suddenly a video advertising a new store opening was downloaded to their device. What kind of attack was the mobile user subjected to? Select one: Bluesnarfing Bluejacking Worm Rootkit Although PenTesters are in the middle of an attack, they supply the organization with the report identifying findings. What did the Pentesters report on? Select one: Indicators of prior compromise Critical findings Goal reprioritization Status report An organization is using mobile device management to ensure that its mobile infrastructure is secure. What are some common features mobile device management solutions? (Select all that apply.) Select one or more: Fingerprint login Remote lock Encrypted containers Profiles A PenTester discovered a compromise to a financial institution's systems and uncovers that the systems may have compromised for years. What kind of exploit did the Pentester uncover? Select one: Backdoor Bind shell APT Daemon