Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Arrange and connect the cybersecurity principles according to how you view their relationship. Complete mediation Defense in depth Encapsulation Fail safe default Isolation Simplicity of
Arrange and connect the cybersecurity principles according to how you view their relationship. 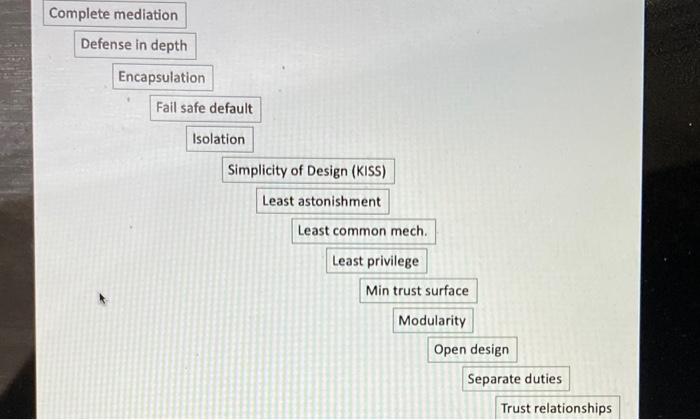
Complete mediation Defense in depth Encapsulation Fail safe default Isolation Simplicity of Design (KISS) Least astonishment Least common mech. Least privilege Min trust surface Modularity Open design Separate duties Trust relationships 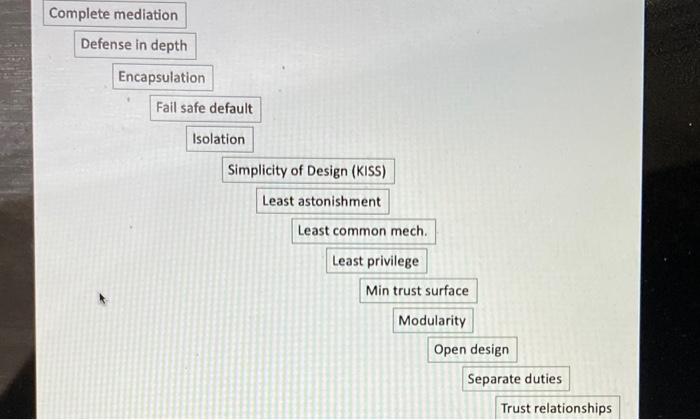
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started