Can you help me solving this problem?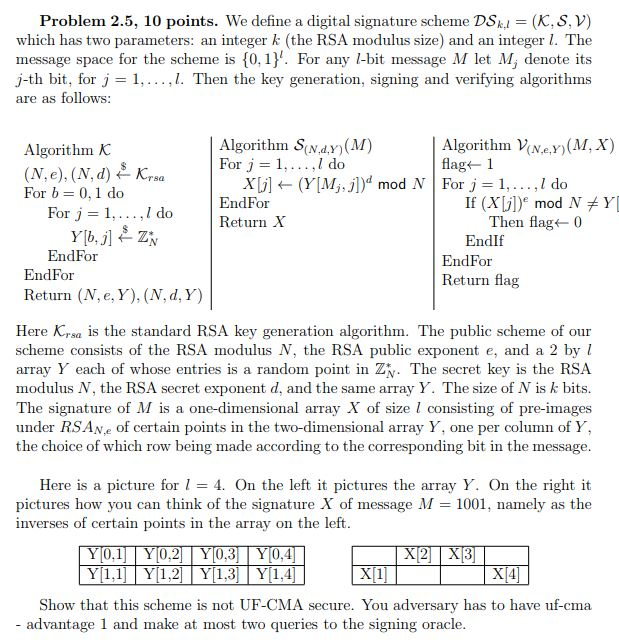
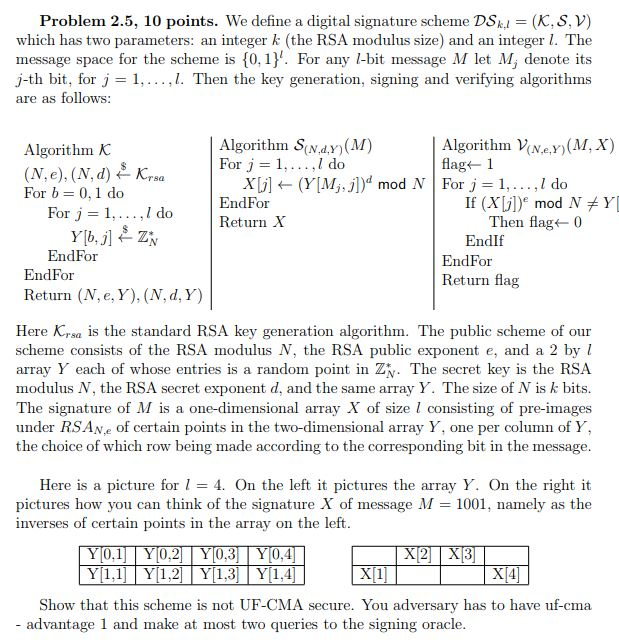
Problem 2.5, 10 points. We define a digital signature scheme DSk- (K, S, V) which has two parameters: an integer k (the RSA modulus size) and an integer 1. The message space for the scheme is [0, 1) For any l-bit message M let M, denote its j-th bit, for j = 1, ,L Then the key generation, signing and verifying algorithms are as follows: Algorithm V(Ne.y)(M, Algorithm SNdy)(M) For j = 1, . . . . I do Algorithm K xLi] (Y[My])" mod N. | For J = 1, EndFor Return X , I do For b = 0.1 do If (X[j])" mod N For j = 1, ,Ido Then flag 0 EndIf EndFor EndFor EndFor Return flag Return (N, e, Y), (N, d, Y) Here Krsa is the standard RSA key generation algorithm. The public scheme of our scheme consists of the RSA modulus N, the RSA public exponent e, and a 2 by l array Y each of whose entries is a random point in Z\. The secret key is the RSA modulus N, the RSA secret exponent d, and the same array Y. The size of N is k bits. The signature of M is a one-dimensional array X of size I consisting of pre-images under RSANe of certain points in the two-dimensional array Y, one per column of Y the choice of which row being made according to the corresponding bit in the message Here is a picture for l = 4, On the left it pictures the array Y. On the right it pictures how you can think of the signature X of message M = 1001, namely as the inverses of certain points in the array on the left 0.2 0,4 XI4 Show that this scheme is not UF-CMA secure. You adversary has to have uf-cma advantage 1 and make at most two queries to the signing oracle Problem 2.5, 10 points. We define a digital signature scheme DSk- (K, S, V) which has two parameters: an integer k (the RSA modulus size) and an integer 1. The message space for the scheme is [0, 1) For any l-bit message M let M, denote its j-th bit, for j = 1, ,L Then the key generation, signing and verifying algorithms are as follows: Algorithm V(Ne.y)(M, Algorithm SNdy)(M) For j = 1, . . . . I do Algorithm K xLi] (Y[My])" mod N. | For J = 1, EndFor Return X , I do For b = 0.1 do If (X[j])" mod N For j = 1, ,Ido Then flag 0 EndIf EndFor EndFor EndFor Return flag Return (N, e, Y), (N, d, Y) Here Krsa is the standard RSA key generation algorithm. The public scheme of our scheme consists of the RSA modulus N, the RSA public exponent e, and a 2 by l array Y each of whose entries is a random point in Z\. The secret key is the RSA modulus N, the RSA secret exponent d, and the same array Y. The size of N is k bits. The signature of M is a one-dimensional array X of size I consisting of pre-images under RSANe of certain points in the two-dimensional array Y, one per column of Y the choice of which row being made according to the corresponding bit in the message Here is a picture for l = 4, On the left it pictures the array Y. On the right it pictures how you can think of the signature X of message M = 1001, namely as the inverses of certain points in the array on the left 0.2 0,4 XI4 Show that this scheme is not UF-CMA secure. You adversary has to have uf-cma advantage 1 and make at most two queries to the signing oracle