DES-like cipher
CAN YOU PLEASE DO THIS (java)
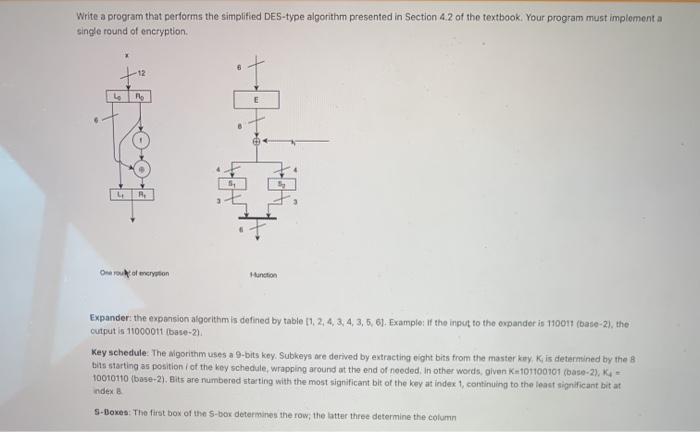
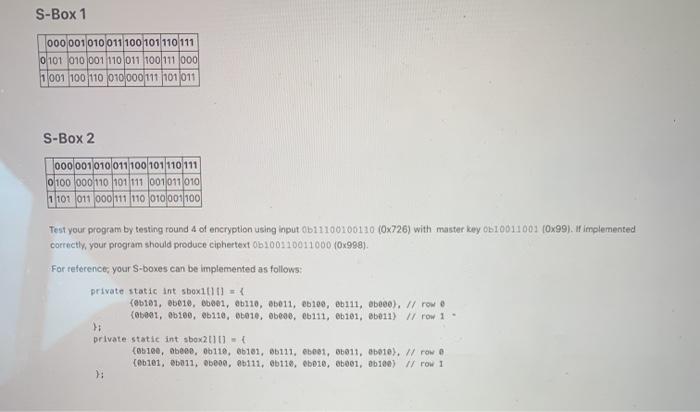
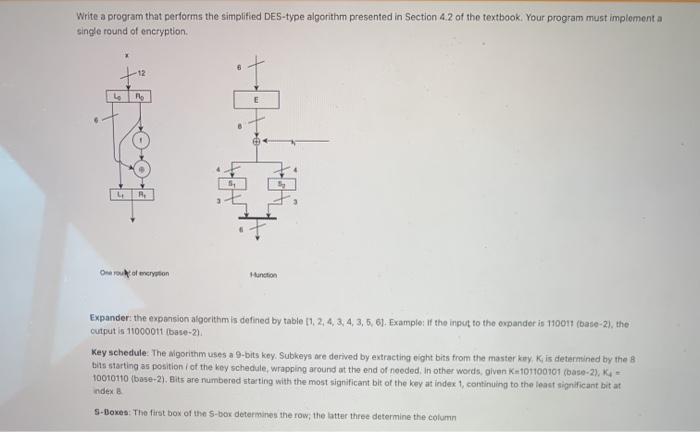
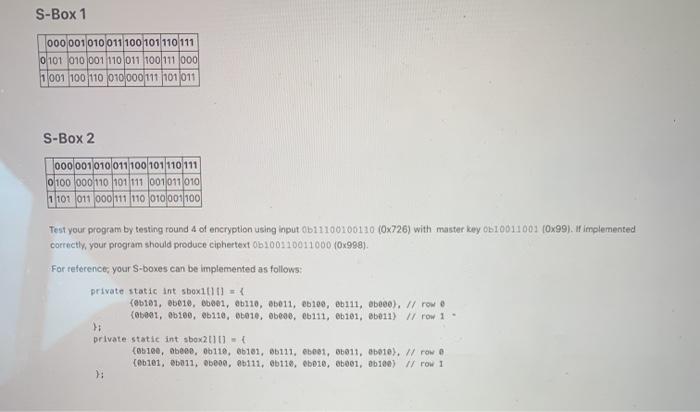
Write a program that performs the simplified DES-type algorithm presented in Section 4.2 of the textbook. Your program must implement a single round of encryption +12 R E R Oroscryption Hunction Expander: the expansion algorithm is defined by table 1, 2, 4, 3, 4, 5, 6, 6). Example: If the input to the expander is 110011(base-2), the output is 11000011 buce-21 Key schedule. The Nigorithm uses a 9-bits key. Subkeys are derived by extracting eight bits from the master kay Ki is determined by the 8 bits starting as position of the key schedule, wrapping around at the end of needed. In other words, given K-101100101 (base-2), K- 10010110 (base-2). Bits are numbered starting with the most significant bit of the boy at index 1, continuing to the least significant bit at Index S-Boxen: The first box of the S-box determines the row, the latter three determine the column S-Box 1 000001010011 100 101 110111 0 101 010 001110 011 100111 000 1001 100 110 010000111101011 S-Box 2 000 001010011100101110111 0 100 000 110 101111 001011010 1 101 011 000111110 010001100 Test your program by testing round 4 of encryption using input 0111100100120 (0x726) with master key Ob10011002 (0x99). If implemented correctly, your program should produce ciphertext 0100110011000 70x998). For reference, your S-boxes can be implemented as follows: private static int shox100 = { (0b101, 06010, 66001, 6b110, 6011, e6190, eb111, ebeee), // rowo (05001, 06100, 06110, 06010, obcov. 06111, 0101, 6011) Il row 1 private static int sbox2010) - (06100, obene, 06110, 66101, 06111, 601, 6011, 06010). W rowe (8b101, 6011, obeon, 86111, 06110, 06010, 86001, db100) // row 1 Expectations for code 1. Your code must run in Moodle so I can check that it is valid 2. Solutions must be "clean": correct answers, no warnings, no debugging output 3. Implementation must be structured correctly using functions, variables, constants, etc. 4. Hard coding values is only allowed in unit tests and/or driver classes. All developed code must be general-purpose 5. Collaboration must be attributed in comments 6. Other comments only needed to illustrate program flow, to explain complex constructs, or for leaving pointers for yourselt. "Comment for the sake of comment is not needed