Hey guys need help with these questions
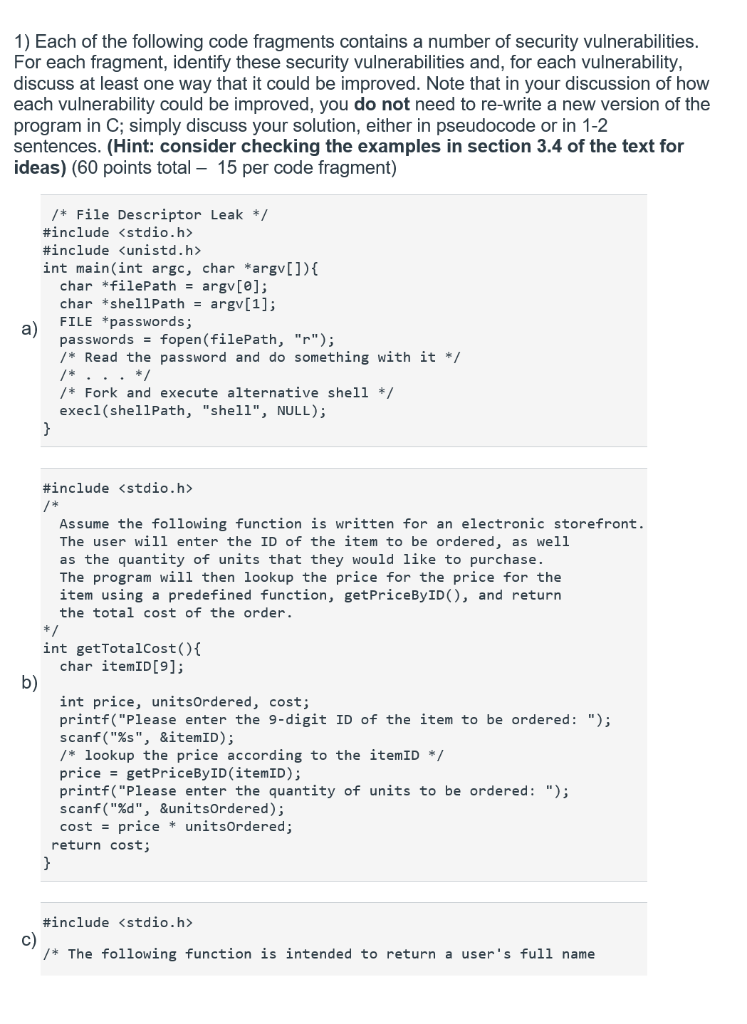
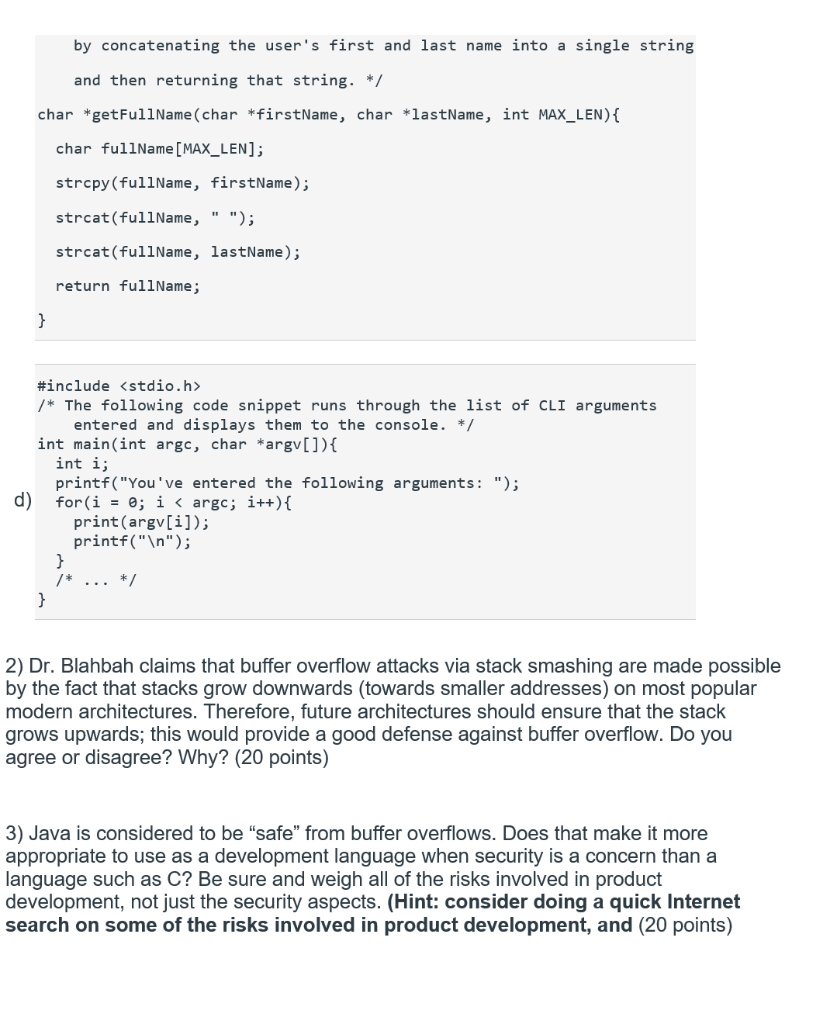
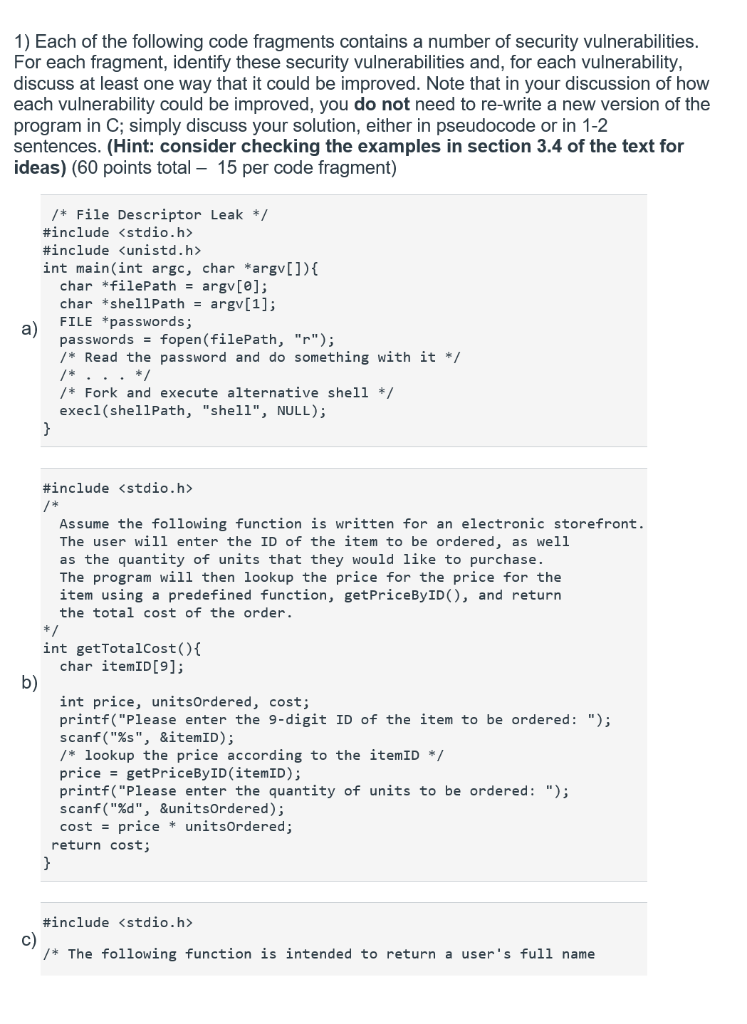
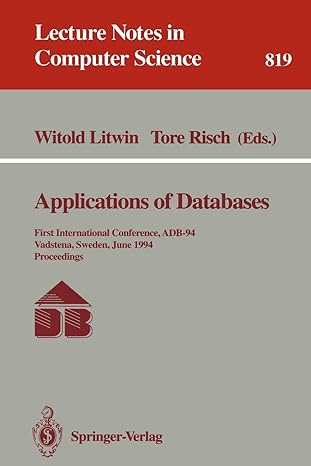
1) Each of the following code fragments contains a number of security vulnerabilities For each fragment, identify these security vulnerabilities and, for each vulnerability discuss at least one way that it could be improved. Note that in your discussion of how each vulnerability could be improved, you do not need to re-write a new version of the program in C; simply discuss your solution, either in pseudocode or in 1-2 sentences. (Hint: consider checking the examples in section 3.4 of the text for ideas) (60 points total 15 per code fragment) /* File Descriptor Leak/ #include
#include int main(int argc, char *argv[]) char *filePath argv[e]; char *shellPathargv[1]; FILE *passwords; passwordsfopen(filePath, "r") /* Read the password and do something with it */ a) /Fork and execute alternative shell execl(shellPath, "shel11", NULL) #include Assume the following function is written for an electronic storefront. The user will enter the ID of the item to be ordered, as well as the quantity of units that they would like to purchase. The program will then lookup the price for the price for the item using a predefined function, getPriceByID), and return the total cost of the order. int getTotalCost() char itemID[9]; b) int price, unitsOrdered, cost; printf("Please enter the 9-digit ID of the item to be ordered:" scanf("%s", aitem1D); /*lookup the price according to the itemID */ price - getPriceByID (itemID); printf( "Please enter the quantity of units to be ordered: "); scanf("%d", &unitsOrdered); cost price unitsOrdered; return cost #include c) /The following function is intended to return a user's full name by concatenating the user's first and last name into a single string and then returning that string.*/ char *getFullName (char*firstName, char *lastName, int MAX_LEN) char fullName [MAX LEN]; strcpy (fullName, firstName); strcat(fullName, " "); strcat(fullName, lastName) return fullName; #include /The following code snippet runs through the list of CLI arguments entered and displays them to the console* int main(int argc, char *argv[]) int i printf("You 've entered the following arguments: "); print(argv[i]) printf("In"); 2) Dr. Blahbah claims that buffer overflow attacks via stack smashing are made possible by the fact that stacks grow downwards (towards smaller addresses) on most popular modern architectures. Therefore, future architectures should ensure that the stack grows upwards; this would provide a good defense against buffer overflow. Do you agree or disagree? Why? (20 points) 3) Java is considered to be "safe" from buffer overflows. Does that make it more appropriate to use as a development language when security is a concern than a language such as C? Be sure and weigh all of the risks involved in product development, not just the security aspects. (Hint: consider doing a quick Internet search on some of the risks involved in product development, and (20 points)