Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Review the threats and corresponding attacks in Table 2-1 in your textbook. How would you prioritize these threats and attacks as they relate to the
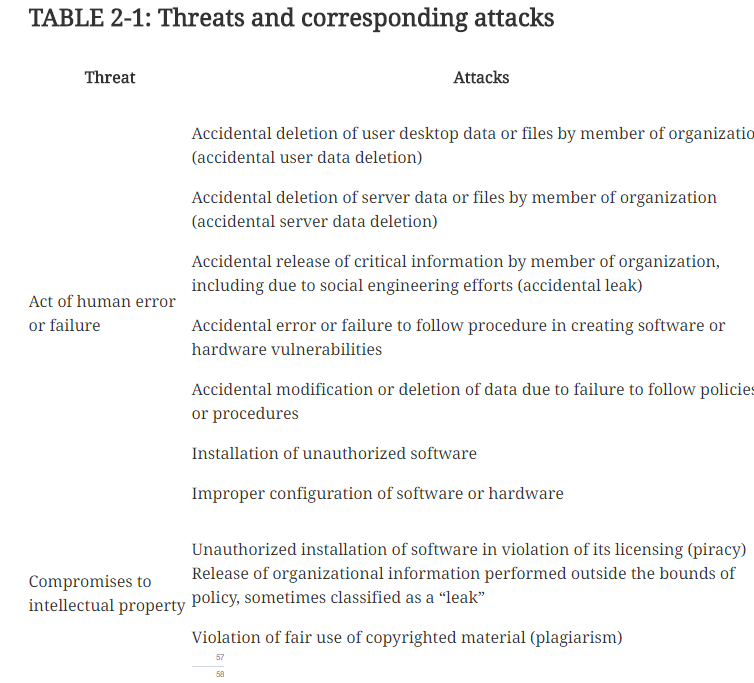
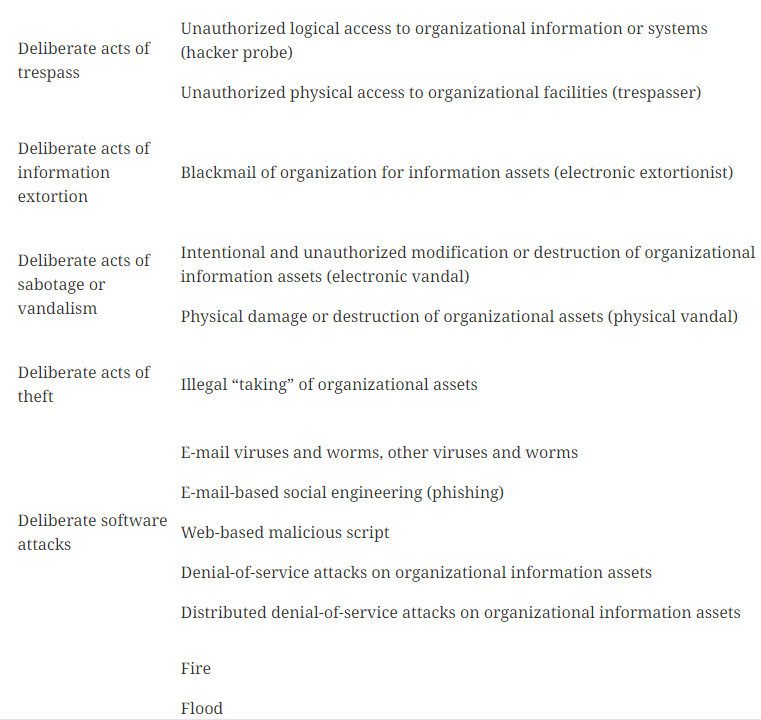
Review the threats and corresponding attacks in Table 2-1 in your textbook. How would you prioritize these threats and attacks as they relate to the computer network at your home, place of work, and/or a school's computer laboratory? Explain the rationale for how you arrived at your conclusions.
TABLE 2-1: Threats and corresponding attacks Threat Attacks Accidental deletion of user desktop data or files by member of organizatio (accidental user data deletion) Accidental deletion of server data or files by member of organization (accidental server data deletion) Accidental release of critical information by member of organization, including due to social engineering efforts (accidental leak) Act of human error Accidental error or failure to follow procedure in creating software or or failure hardware vulnerabilities Accidental modification or deletion of data due to failure to follow policies or procedures Installation of unauthorized software Improper configuration of software or hardware Unauthorized installation of software in violation of its licensing (piracy) Compromises to Release of organizational information performed outside the bounds of policy, sometimes classified as a "leak" intellectual property Violation of fair use of copyrighted material (plagiarism)Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started