Question
this is circularlinkedlist.java package circularlinkedlist; import java.util.Iterator; public class CircularLinkedList implements Iterable { // Your variables Node head; Node tail; int size; // BE SURE
this is circularlinkedlist.java
package circularlinkedlist; import java.util.Iterator;
public class CircularLinkedList
// Your variables Node
// implement this constructor public CircularLinkedList() { }
// I highly recommend using this helper method // Return Node
return null; }
// attach a node to the end of the list public boolean add(E item) { this.add(size,item); return false;
}
// Cases to handle // out of bounds // adding to empty list // adding to front // adding to "end" // adding anywhere else // REMEMBER TO INCREMENT THE SIZE public void add(int index, E item){
}
// remove must handle the following cases // out of bounds // removing the only thing in the list // removing the first thing in the list (need to adjust the last thing in the list to point to the beginning) // removing the last thing // removing any other node // REMEMBER TO DECREMENT THE SIZE public E remove(int index) { return null; } // Turns your list into a string // Useful for debugging public String toString(){ Node
// returns true if there is a next node // this is always should return true if the list has something in it public boolean hasNext() { // TODO Auto-generated method stub return size != 0; } // advances the iterator to the next item // handles wrapping around back to the head automatically for you public E next() { // TODO Auto-generated method stub prev = nextItem; nextItem = nextItem.next; index = (index + 1) % size; return prev.item; } // removed the last node was visted by the .next() call // for example if we had just created a iterator // the following calls would remove the item at index 1 (the second person in the ring) // next() next() remove() public void remove() { int target; if(nextItem == head) { target = size - 1; } else{ target = index - 1; index--; } CircularLinkedList.this.remove(target); //calls the above class } } // It's easiest if you keep it a singly linked list // SO DON'T CHANGE IT UNLESS YOU WANT TO MAKE IT HARDER private static class Node
this is SolitaireEncryption.java
public class SolitaireEncryption {
public static char encryptChar(char letter, int key) { int value = letter - 'a'; int encryptedValue = (value + key) % 26; char encryptedChar = (char) (encryptedValue+'a');
return encryptedChar; }
public static char decryptChar(char letter, int key) { int value = letter - 'a'; int decryptedValue = (value + (26-key)) % 26; char decryptedChar = (char) (decryptedValue+'a');
return decryptedChar; }
public int getKey(CircularLinkedList
private static void step1(CircularLinkedList
private static void step2(CircularLinkedList
} private static void step3(CircularLinkedList
} private static void step4(CircularLinkedList
} private static int step5(CircularLinkedList
public static void main(String[] args) { CircularLinkedList
If you can, could you show the code through IntelliJ? thank you so much for your help.
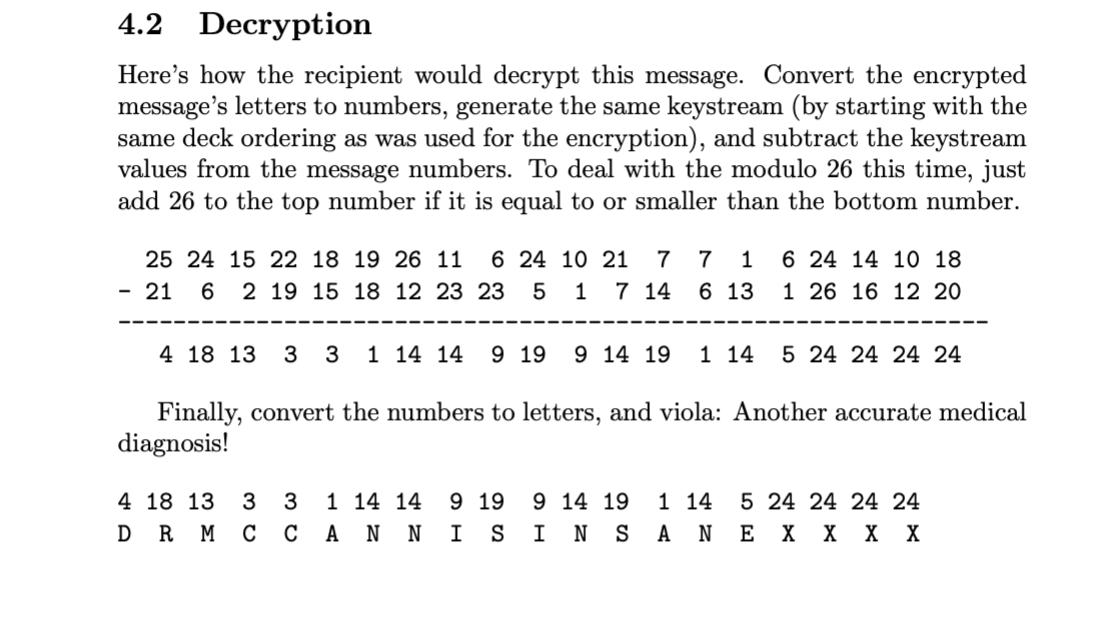
4.2 Decryption Here's how the recipient would decrypt this message. Convert the encrypted message's letters to numbers, generate the same keystream (by starting with the same deck ordering as was used for the encryption), and subtract the keystream values from the message numbers. To deal with the modulo 26 this time, just add 26 to the top number if it is equal to or smaller than the bottom number. 7 1 25 24 15 22 18 19 26 11 6 24 10 21 7 - 21 6 2 19 15 18 12 23 23 5 1 7 14 6 24 14 10 18 1 26 16 12 20 6 13 4 18 13 3 3 1 14 14 9 19 9 14 19 1 14 5 24 24 24 24 Finally, convert the numbers to letters, and viola: Another accurate medical diagnosis! 4 18 13 3 D RMC 3 C 1 14 14 9 19 S 9 14 19 INS 1 14 AN 5 24 24 24 24 E X X X X 5 Assignment Use CircularLinkedList.java as a starting point to make a new program that reads in a 'deck' of 28 numbers (from a file, from a command line, or an array, your choice), asks the user for one or more messages to decrypt, and decrypts them using the modified Solitaire algorithm described above. Note that if your program is decrypting multiple messages, all but the first should be decrypted using the deck as it exists after the decryption of the previous message. (The first uses the deck provided, of course.) 5.1 Why a Circular Linked List? We use Circular Linked List here for a few reasons Good practice solving and thinking for the upcoming exam. The wrap around nature of the Circular Linked List allows us to not worry about Steps 1 and 2. Linked Lists are ideal for these kinds of manipulations, as we can move entire sections of the list around much, much quicker than an ArrayList. For example, in step 3, we can split our deck into multiple smaller decks and recombine them very quickly. 5.2 Output Your output will be just the decrypted messages spaces or punctuation. lists of characters without 5.3 Want to Learn More? The original Solitaire algorithm is described on this web page: http://www.schneier.com/solitaire.html. 4.2 Decryption Here's how the recipient would decrypt this message. Convert the encrypted message's letters to numbers, generate the same keystream (by starting with the same deck ordering as was used for the encryption), and subtract the keystream values from the message numbers. To deal with the modulo 26 this time, just add 26 to the top number if it is equal to or smaller than the bottom number. 7 1 25 24 15 22 18 19 26 11 6 24 10 21 7 - 21 6 2 19 15 18 12 23 23 5 1 7 14 6 24 14 10 18 1 26 16 12 20 6 13 4 18 13 3 3 1 14 14 9 19 9 14 19 1 14 5 24 24 24 24 Finally, convert the numbers to letters, and viola: Another accurate medical diagnosis! 4 18 13 3 D RMC 3 C 1 14 14 9 19 S 9 14 19 INS 1 14 AN 5 24 24 24 24 E X X X X 5 Assignment Use CircularLinkedList.java as a starting point to make a new program that reads in a 'deck' of 28 numbers (from a file, from a command line, or an array, your choice), asks the user for one or more messages to decrypt, and decrypts them using the modified Solitaire algorithm described above. Note that if your program is decrypting multiple messages, all but the first should be decrypted using the deck as it exists after the decryption of the previous message. (The first uses the deck provided, of course.) 5.1 Why a Circular Linked List? We use Circular Linked List here for a few reasons Good practice solving and thinking for the upcoming exam. The wrap around nature of the Circular Linked List allows us to not worry about Steps 1 and 2. Linked Lists are ideal for these kinds of manipulations, as we can move entire sections of the list around much, much quicker than an ArrayList. For example, in step 3, we can split our deck into multiple smaller decks and recombine them very quickly. 5.2 Output Your output will be just the decrypted messages spaces or punctuation. lists of characters without 5.3 Want to Learn More? The original Solitaire algorithm is described on this web page: http://www.schneier.com/solitaire.htmlStep by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started