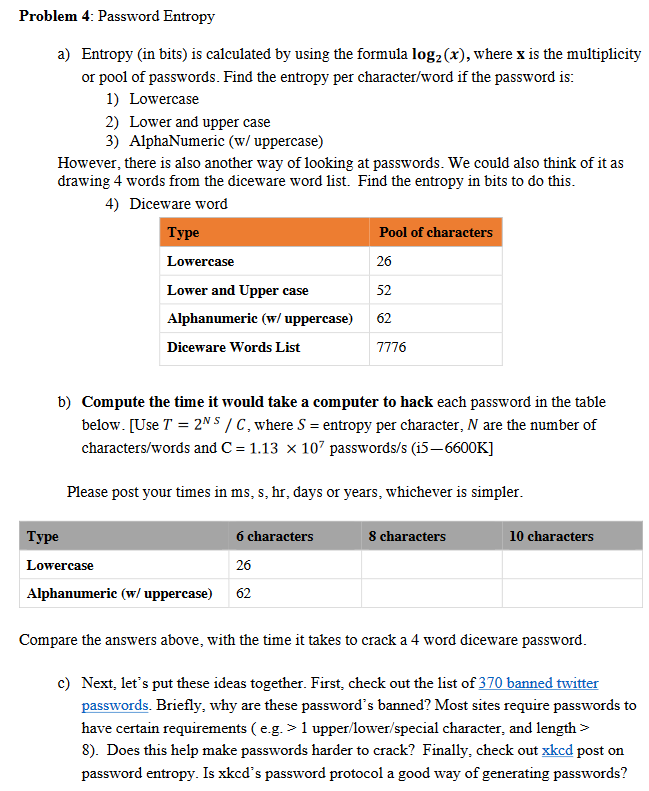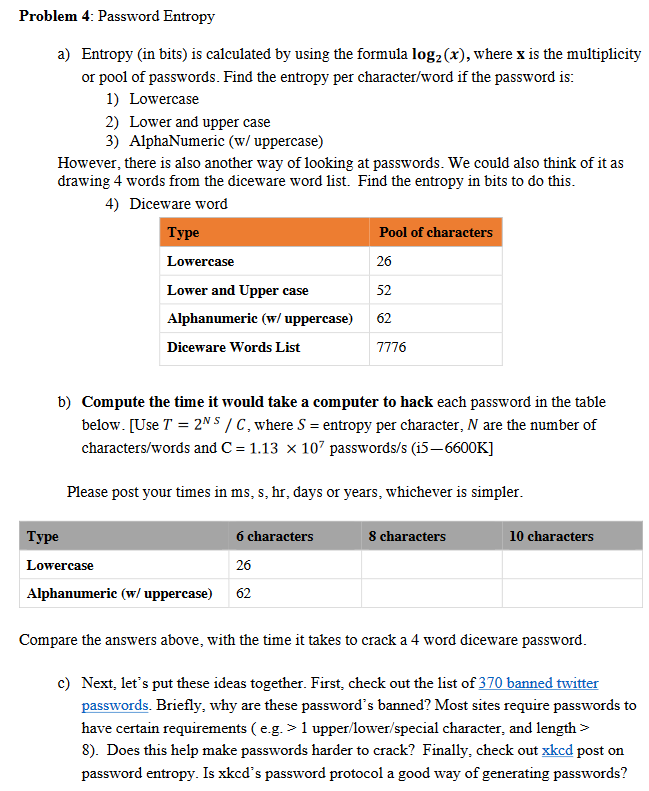
Problem 4: Password Entropy a) Entropy (in bits) is calculated by using the formula logz(x), where x is the multiplicity or pool of passwords. Find the entropy per character/word if the password is: 1) Lowercase 2) Lower and upper case 3) AlphaNumeric (w/ uppercase) However, there is also another way of looking at passwords. We could also think of it as drawing 4 words from the diceware word list. Find the entropy in bits to do this. 4) Diceware word Type Pool of characters Lowercase 26 Lower and Upper case Alphanumeric (w/ uppercase) Diceware Words List 52 62 7776 b) Compute the time it would take a computer to hack each password in the table below. [Use T = 2NS / C, where S = entropy per character, N are the number of characters/words and C= 1.13 x 107 passwords/s (i5-6600K] Please post your times in ms, s, hr, days or years, whichever is simpler. Type 8 characters 10 characters Lowercase 6 characters 26 62 Alphanumeric (w/ uppercase) Compare the answers above, with the time it takes to crack a 4 word diceware password. c) Next, let's put these ideas together. First, check out the list of 370 banned twitter passwords. Briefly, why are these password's banned? Most sites require passwords to have certain requirements (e.g. > 1 upper/lower/special character, and length > 8). Does this help make passwords harder to crack? Finally, check out xkcd post on password entropy. Is xkcd's password protocol a good way of generating passwords? Problem 4: Password Entropy a) Entropy (in bits) is calculated by using the formula logz(x), where x is the multiplicity or pool of passwords. Find the entropy per character/word if the password is: 1) Lowercase 2) Lower and upper case 3) AlphaNumeric (w/ uppercase) However, there is also another way of looking at passwords. We could also think of it as drawing 4 words from the diceware word list. Find the entropy in bits to do this. 4) Diceware word Type Pool of characters Lowercase 26 Lower and Upper case Alphanumeric (w/ uppercase) Diceware Words List 52 62 7776 b) Compute the time it would take a computer to hack each password in the table below. [Use T = 2NS / C, where S = entropy per character, N are the number of characters/words and C= 1.13 x 107 passwords/s (i5-6600K] Please post your times in ms, s, hr, days or years, whichever is simpler. Type 8 characters 10 characters Lowercase 6 characters 26 62 Alphanumeric (w/ uppercase) Compare the answers above, with the time it takes to crack a 4 word diceware password. c) Next, let's put these ideas together. First, check out the list of 370 banned twitter passwords. Briefly, why are these password's banned? Most sites require passwords to have certain requirements (e.g. > 1 upper/lower/special character, and length > 8). Does this help make passwords harder to crack? Finally, check out xkcd post on password entropy. Is xkcd's password protocol a good way of generating passwords